OPERATIONALIZED
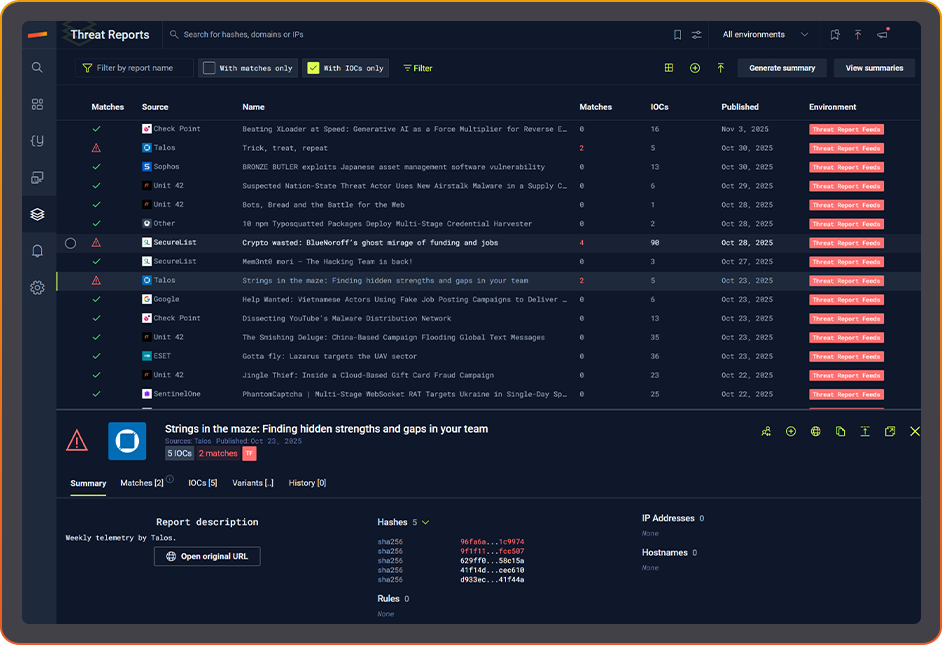
THREAT INTELLIGENCE
Continuously connects new threat intelligence to your environment so security teams detect more threats, investigate faster, and reduce manual work.
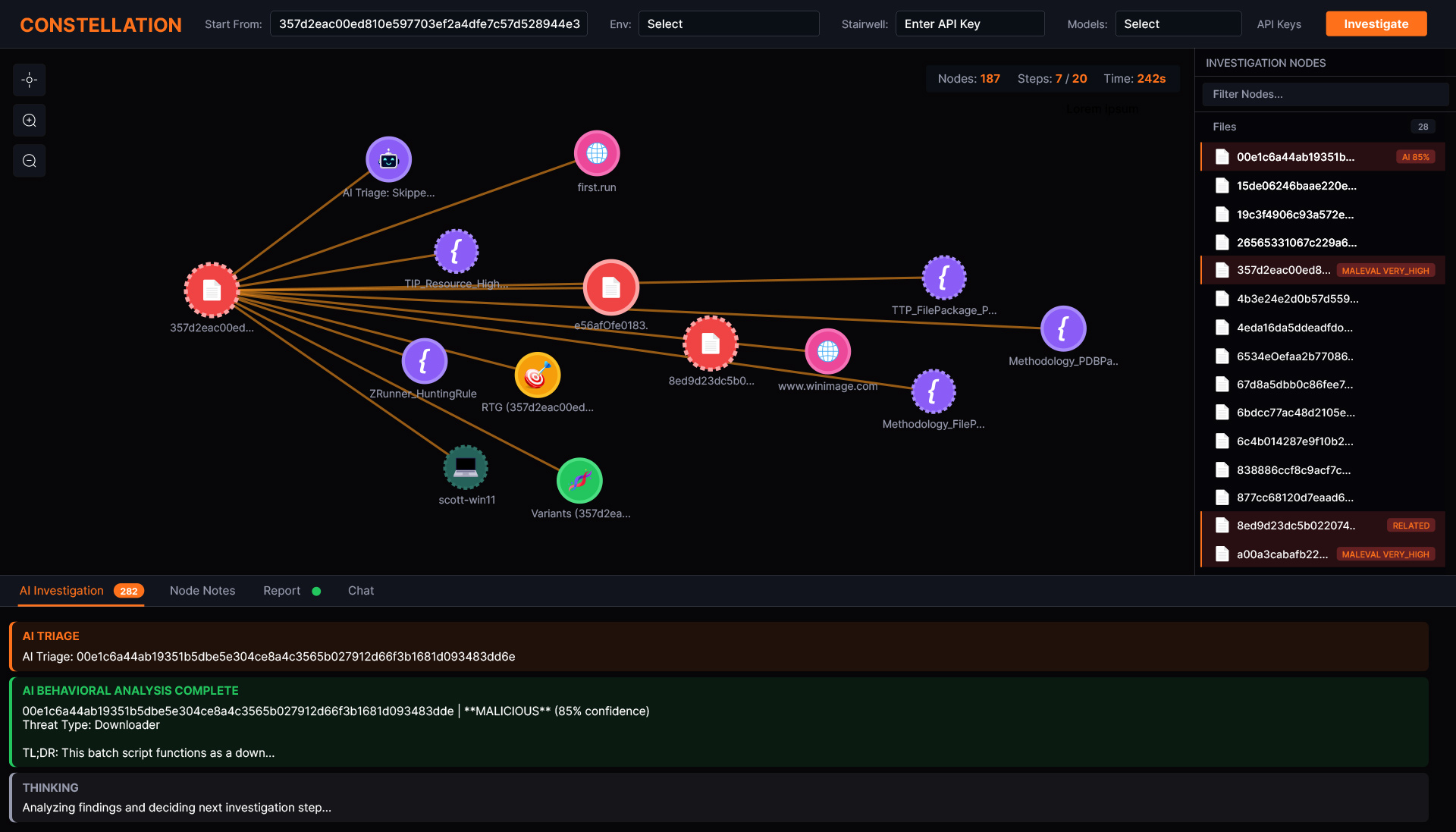
FASTER AGENTIC INVESTIGATIONS
Investigate any alert or IOC and go from a single signal to a constellation of connected threats in seconds.
YOU’RE IN GOOD COMPANY






CONCLUSIVE INVESTIGATIONS
200
SECONDS
EXPANDED
DETECTIONS
157%
MORE HIDDEN MALWARE
AGENTIC
INVESTIGATIONS
AT SCALE
SOC WORKFLOW
HOURS SAVED
60%
THREAT INTELLIGENCE BREAKS DOWN WHEN IT
STAYS TRAPPED IN DIFFERENT TOOLS
CTI tool sprawl
slows workflow processes
Detection gaps
from siloed tools and workflows
Fragmented telemetry not propagated to your environment
Alert overload
of low-value alerts
Lack of alert risk context means prioritization is impossible
STAIRWELL DELIVERS
ONE PLATFORM TO OPERATIONALIZE THREAT INTELLIGENCE
DETECT MORE THREATS
INVESTIGATE FASTER
SAVE TIME AND MONEY
Cut manual effort while simplifying workflows and reducing tool spend.
INSTANT ANSWERS TO YOUR TOUGHEST SECURITY QUESTIONS.
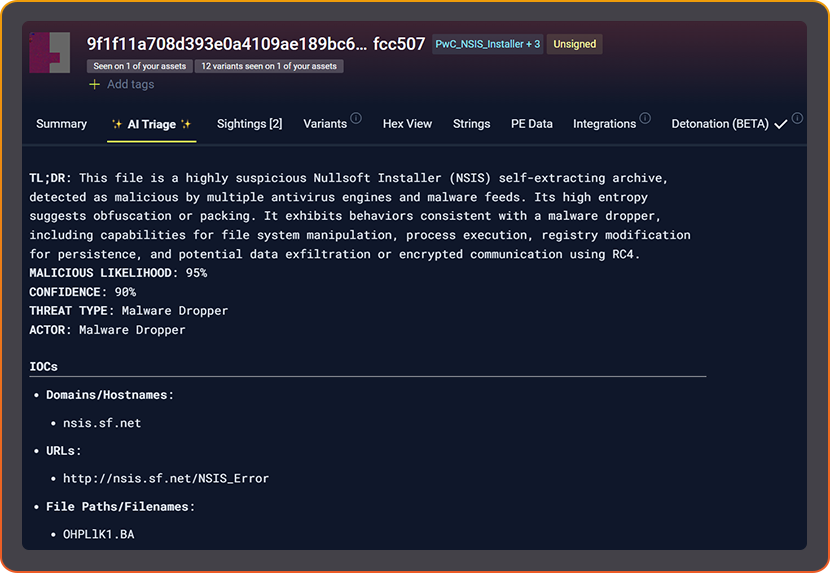
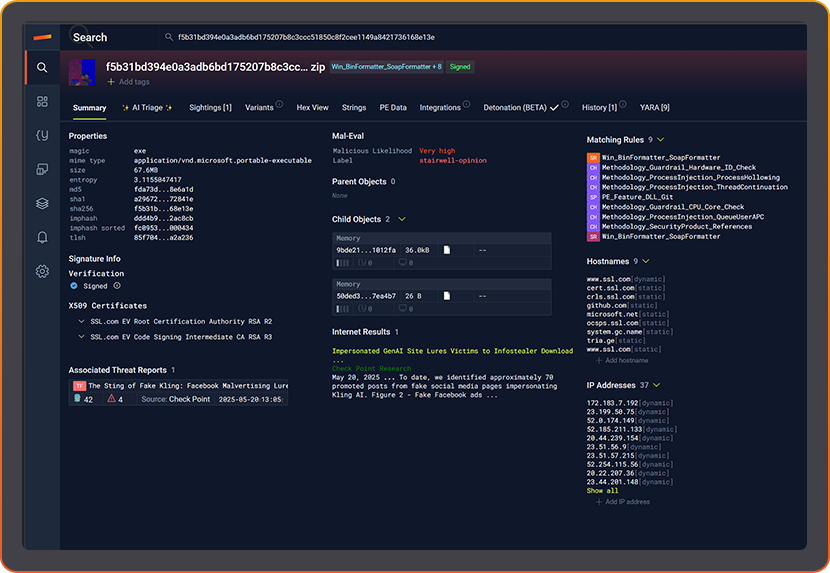
Is this file bad?
ANSWER YOUR TEAM’S QUESTIONS. ALL IN ONE PLACE.
Each member of your team answers different questions using Stairwell.
- Is this file bad?
- How do I triage an alert?
- Do we have that hash anywhere?
- I need a second opinion on this EDR alert?
- Any IP addresses in that file?
- Any hostnames associated with that file?
- Is that file signed?
- How many machines have seen that file?
- Is this file bad?
- What are the historic resolutions of that domain?
- Any IOCs from these threat reports in my enterprise?
- Any YARA rules triggered by that file?
- Do any files in my enterprise trigger any YARA rules?
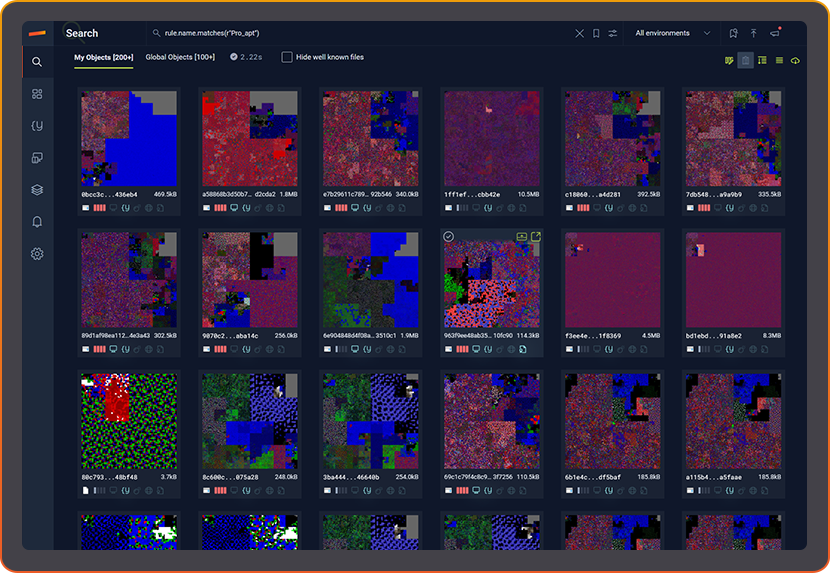
- Are there variants of that malware anywhere?
- What other files are part of that malware campaign?
- Which other devices saw those files?
- What other files were on that machine on that date?
- Which devices contain Log4J?
- Which devices have unauthorized software?
FROM NEW INTELLIGENCE TO ACTION IN SECONDS
GATHER
Bring together signals from threat feeds, malware analysis, published threat reports, DNS, YARA, and connect to your enterprise files.
DETECT
INVESTIGATE
Expert agentic investigations are faster and go from a single alert to a constellation of threats.
RESPOND
Understand what is present, what was, and what matters so teams prioritize and act with confidence.
EVERY FILE.
EVERY DEVICE.
UNLIMITED RETENTION AND CONSISTENCY
CONNECTED TO
YOUR ASSETS
PRIVATE THREAT INTELLIGENCE
Stairwell makes threat intelligence sovereign
PRIVATE. CONTINUOUS. YOURS
Cybersecurity Expert, Hospitality
WHY STAIRWELL IS DIFFERENT
Operationalizes CTI at scale
Connects CTI to your files
Detects what other
tools miss
Agentic Investigation
Continuous in a private environment
KEY FEATURES
Core capabilities of Stairwell’s malware and threat intelligence platform.
AI TRIAGE & MALWARE ANALYSIS
AI Triage steps outside the sandbox.
KEY BENEFITS
- Explains behavior, context, and intent instantly.
- Accelerates analyst triage and adjudication.
- Turns malware analysis into explainable intelligence.
MALWARE VARIANT DISCOVERY
Find what looks like other malware.
KEY BENEFITS
- Identifies polymorphic malware and re-used tooling.
- Builds family trees of related malware samples.
- Enables proactive variant-aware detection
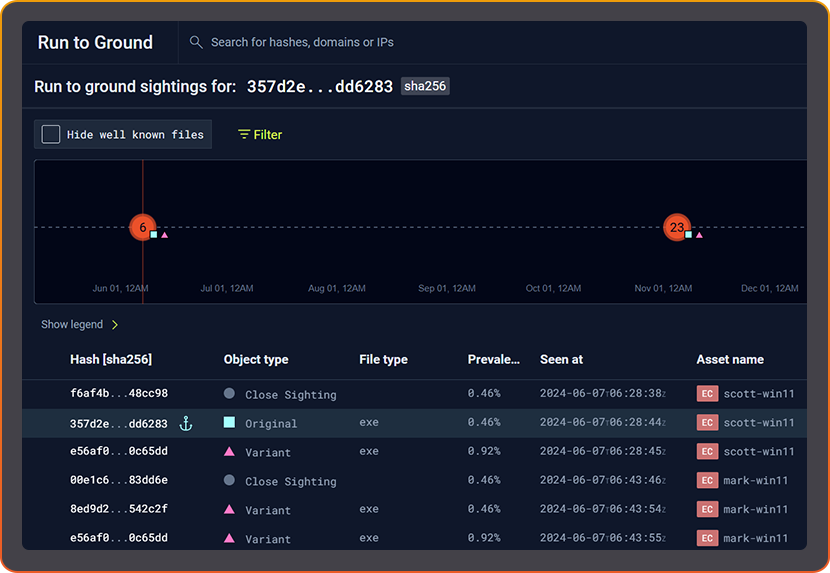
INSTANT INVESTIGATION WITH RUN TO GROUND
One click. Every variant. Every Trace.
KEY BENEFITS
- Enrich any EDR detection with full variant context.
- Connect related activity across time and hosts.
- Delivers forensics-level investigation capability to Tier-1 SOCs.
PRIVATE VAULT FOR YOUR DATA
Your data. Your Hindsight.
Preserve every executable. Continuously scan your own environment with the latest threat intelligence. Global visibility that never leaves your control.
KEY BENEFITS
- Permanent inventory of enterprise executables.
- Continuous retroactive detection as intel evolves.
- Encrypted, isolated storage for compliant visibility.
MALWARE THREAT INTELLIGENCE. RE-IMAGINED.
OLD WAY
- Crowdsourced
- Point-in-time retro hunts
- Public uploads
- Verdicts and labels
- Rising costs (2–10×)
STAIRWELL
- Private vault
- Continuous reanalysis
- Private, encrypted environment
- Intent and lineage
- Owned visibility
- Fractional cost, daily use
SIMPLE PATH TO ENTERPRISE VISIBILITY
STEP 1
Low friction integration. Use Stairwell as your private VirusTotal.
STEP 2
Operationalize threat Intelligence to answer questions faster as file volume grows.
STEP 3
Unlock live and historic visibility with continuous analysis across your enterprise.
Stairwell: Private by design.
Continuous by default.
Stairwell: Private by design. Continuous by default.
The next evolution of threat intelligence is here.
PROTECT YOUR ENTERPRISE WITH AI & STAIRWELL THREAT INTELLIGENCE
Watch how Stairwell makes your SOC, Threat Intel, and Incident Response teams faster.
LEARN MORE ABOUT STAIRWELL
FREQUENTLY ASKED QUESTIONS
What is a cyber threat intelligence platform?
A cyber threat intelligence platform collects, stores, and analyzes data about malicious files, infrastructure, and attacker behavior so security teams can make faster, more informed decisions. The core value is correlation: connecting a suspicious file to known malware families, infrastructure, and campaign history without requiring an analyst to manually pivot across multiple tools.
In practice, a threat intelligence platform sits behind your existing EDR and SIEM and answers specific investigation questions. Is this file malicious? Have we seen this indicator before? Which machines are affected? Platforms like Stairwell add continuous reanalysis to the equation, meaning today’s new threat intelligence is automatically applied to files your organization collected months ago, closing gaps that point-in-time lookups miss entirely.
How does a private threat intelligence platform differ from public tools like VirusTotal?
Public threat intelligence tools aggregate data from every organization that submits files, which means your uploads contribute to a shared corpus that any subscriber can query. A private threat intelligence platform keeps your file data inside an isolated environment so adversaries cannot study what you know, and your telemetry does not signal your detection capabilities to attackers.
The operational difference matters most during active incidents. When you submit a sample to a public service, a sophisticated attacker monitoring that service learns you found their malware. A private vault approach stores and analyzes everything inside your own environment, giving your SOC and threat intel teams the same depth of analysis without exposing your hand. Stairwell is built on this model: your data stays in your Private Vault and is never contributed to a shared pool.
What is continuous malware analysis and why does it matter?
Continuous malware analysis means files are re-evaluated automatically whenever new threat intelligence becomes available, rather than only at the moment of first submission. A file that appeared clean six months ago can be re-scored today because a new YARA rule, a newly published IOC, or an emerging malware family connection now links it to known malicious activity.
Most static analysis tools give you a verdict at upload time and stop there. That point-in-time model creates blind spots as the threat landscape shifts. Continuous analysis changes the relationship between intelligence and your file history: when Stairwell ingests a newly published threat report or an updated malware threat intelligence, it reruns that intelligence against every file ever seen in your environment. Threats that were invisible yesterday become visible today without any manual action from your team.
What cybersecurity threat intelligence tools do SOC analysts use every day?
SOC analysts typically rely on a combination of hash lookup services, sandboxes, threat intelligence feeds, EDR platforms, and SIEM alerts to triage incidents. The practical bottleneck is correlation: each tool answers a narrow question, and stitching answers together manually consumes analyst time that could go toward actual investigation.
Threat intelligence tools that reduce pivoting pay the biggest dividends in a SOC environment. When an analyst can take a single hash and immediately see related variants, historical prevalence, associated infrastructure, and a plain-language explanation of what the file does, triage time drops significantly. Stairwell helps reduce the tool spend on siloed point in time tools and is designed to answer these questions in one place, pulling together file analysis, IOC history, DNS resolution data, and YARA matches so the analyst reaches a verdict without context-switching across five different tabs.
How do threat intelligence feeds work in enterprise security operations?
Threat intelligence feeds are structured data streams containing indicators of compromise, including file hashes, IP addresses, domains, and malware signatures, sourced from security vendors, government agencies, ISACs, and internal research. Enterprise security teams ingest these feeds into their SIEM or threat intelligence platform to enrich alerts and identify whether known-bad indicators appear in their environment.
The challenge with raw threat intelligence feeds is operationalization: a feed that delivers ten thousand IOCs per day is only useful if your team can automatically check those indicators against your file history and get a clear answer. Manual copy-paste lookups are not scalable. Platforms that ingest feeds continuously and automatically cross-reference them against your own telemetry turn a data problem into an actionable workflow, surfacing the handful of indicators that actually matter to your organization. Stairwell operationalizes threat intelligence the moment it is received.
What is a Private Vault in the context of threat intelligence?
A Private Vault is an isolated, encrypted storage environment where an organization keeps its own file telemetry, malware samples, YARA rules, and threat intelligence separate from any shared or public corpus. Files in a Private Vault are never exposed to other organizations or to adversaries who might monitor public submission services.
The security benefit of a Private Vault goes beyond confidentiality. When your enterprise files are stored privately and continuously reanalyzed against global threat intelligence, you build a permanent historical record that supports incident response, compliance audits, and threat hunting. If a new threat actor TTP emerges next month, Stairwell can re-evaluate every file your organization has ever seen to determine whether any of them match, turning historical telemetry into a real-time investigation asset rather than an aging log.
How does file prevalence help with alert prioritization?
Prevalence measures how commonly a file appears across endpoints in your environment and globally across a threat intelligence corpus. Files seen on nearly every machine in your organization are almost always benign system components. Files seen on only one or two endpoints, especially if they are also rare globally, deserve much closer scrutiny.
Adding prevalence to your triage workflow gives SOC analysts a fast signal that cuts through alert noise without requiring deep analysis of every file. When Stairwell continuously recalculates both local prevalence (within your enterprise) and global prevalence (across its malware corpus), it surfaces the rare files that warrant attention. This is particularly useful for Tier 1 analysts who need a clear starting point: high global rarity combined with confirmed malicious behavior in related samples is a strong signal to escalate immediately.