New feature: Threat alerts
Remediation is a critical component of effective cybersecurity and requires constant vigilance in order to stay ahead of emerging threats. With the rise of increasingly sophisticated attacks and the complexity of modern IT environments, manual threat detection and response is no longer sufficient. To address this challenge, Stairwell has introduced a new alerting feature that utilizes a decision engine to surface potential malware objects using automated as well as expert-led triggers.
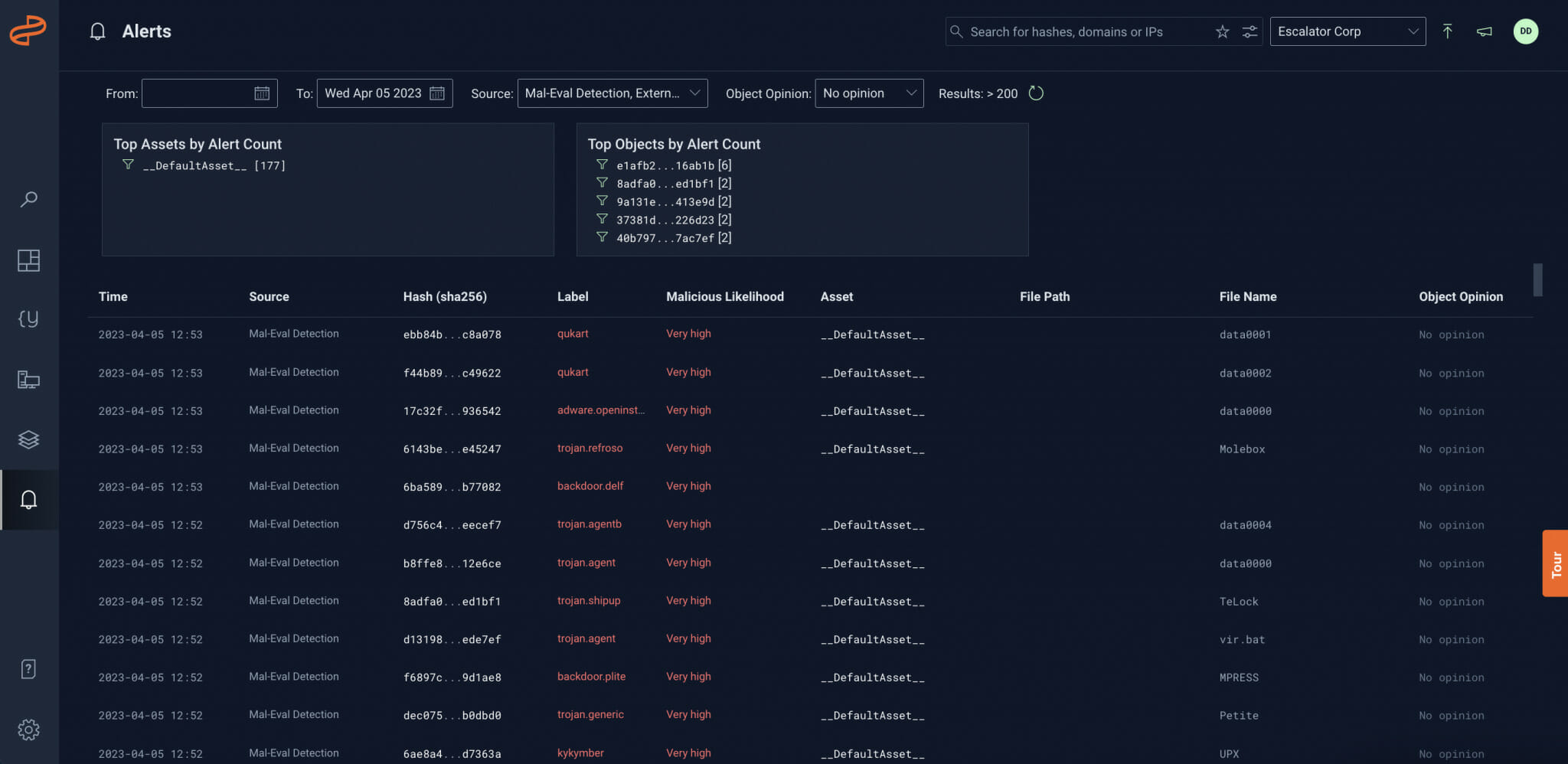
The alerting feature
The new alerting feature in the Stairwell platform builds on the capabilities of our automation as well as expert-led threat Intelligence, allowing security teams to receive real-time alerts based on potential threats. The feature aggregates alerts based on asset and object counts, allows users to set opinions (Trusted, Grayware, Malicious) on objects, and sorts alerts by opinion to view new sightings of objects in that opinion category.
Threat alerts use cases
The alerting feature, decision engine, user opinions, and threat aggregation can be particularly useful in a number of scenarios. For example, security teams can use the feature to quickly identify and respond to threats, track new sightings of grayware, or identify trusted vs. malicious objects. Real-world examples of how these features could be used include identifying and stopping a ransomware attack before it caused significant damage, and assisting an incident response engagement by surfacing initial infection vectors.
Impact on threat response times, SOC auditing, and operational efficiency
The alerting features in the Stairwell platform have a significant impact on threat response times, SOC auditing, operational efficiency, and overall security posture. By providing real-time alerts based on potential threats detected by the decision engine, as well as enabling users to leverage expert-led threat intelligence, security teams can quickly detect and respond to threats, while also improving their remedial efficiency.