MALWARE ANALYSIS
ANALYZE THREAT INTELLIGENCE. CONTINUOUSLY.
Static malware analysis goes stale fast as endpoints change and new executables appear every day.
Stairwell continuously reanalyzes your file history as new threat intelligence arrives, correlates signals across sources, and flags new matches you would have missed yesterday. This is threat intel you can actually use. Because it operationalizes hindsight.
HOW IT WORKS
CONTINUOUS ANALYSIS
Stairwell reanalyzes every data set continuously, so intelligence stays current.
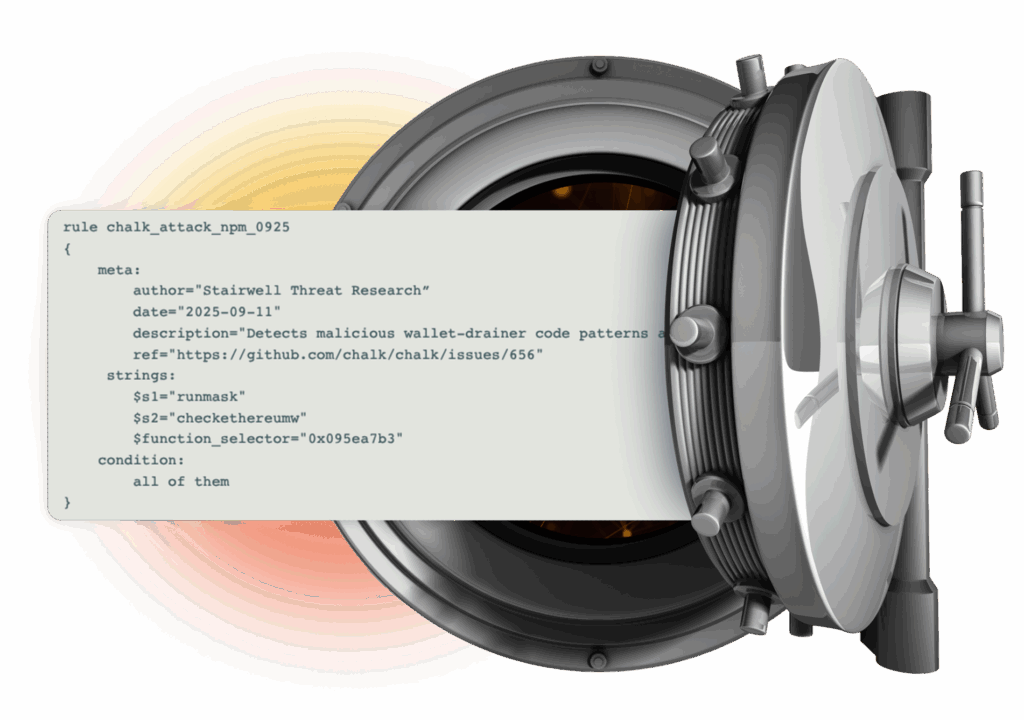
PRIVATE BY DESIGN
Stored in a private vault. Your threat intelligence stays yours, and nobody else’s.
INVISIBLE TO ADVERSARIES
Attackers reverse engineer endpoint tools, but cannot study a SaaS system they cannot access.

SEARCH ENGINE FOR THREAT INTEL
Stairwell is a private search engine for malware within your enterprise executable files. Search what matters most, your own data, to hunt threats, discover new variants, and run deep file forensics without exposing anything publicly.

PRIVATE HASH LOOKUP
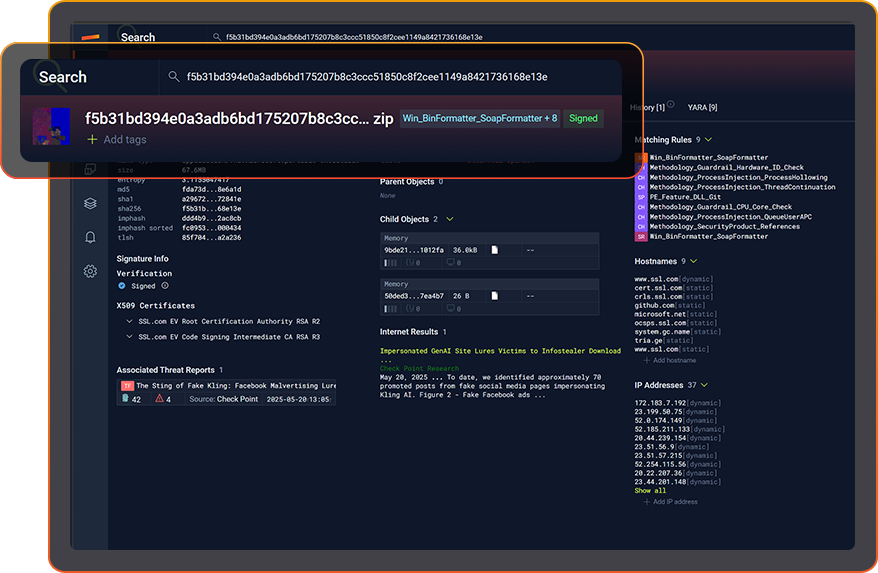
RICHER INTEL. FASTER DECISIONS.
Stairwell captures and analyzes every signal around a file, so your team stops guessing and chasing context.
Hashes, IOCs, IPs, DNS history, hostnames, YARA matches, variants, and more, all land in one place. With continuous re-analysis against newly enriched intelligence, your SOC makes faster calls with more confidence.
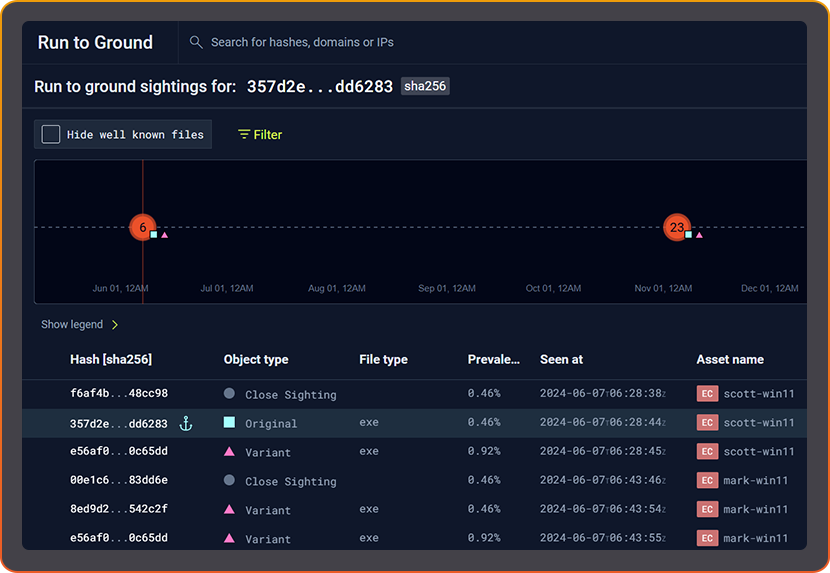
FIND HIDDEN VARIANTS
Stairwell uses your Private Vault plus its Malware Corpus to spot malware variants hiding inside your enterprise.
Variant Discovery turns a single hash into visibility of the entire malware family. In seconds, understand all the infrastructure this malware family used across history. No YARA required.
AUTOMATED FORENSICS. IN SECONDS.

INFECTION TIMELINE. MADE CLEAR.
PREVALENCE. YOUR FASTEST TRIAGE SIGNAL.
Common files on every machine are rarely the problem. Rare files usually are. Stairwell continuously recalculates both local prevalence in your environment and global prevalence across Stairwell, then correlates those signals to guide what deserves attention.
By adding prevalence to your workflow, your SOC can prioritize alerts faster and cut false positives without guessing.
YARA AT SCALE
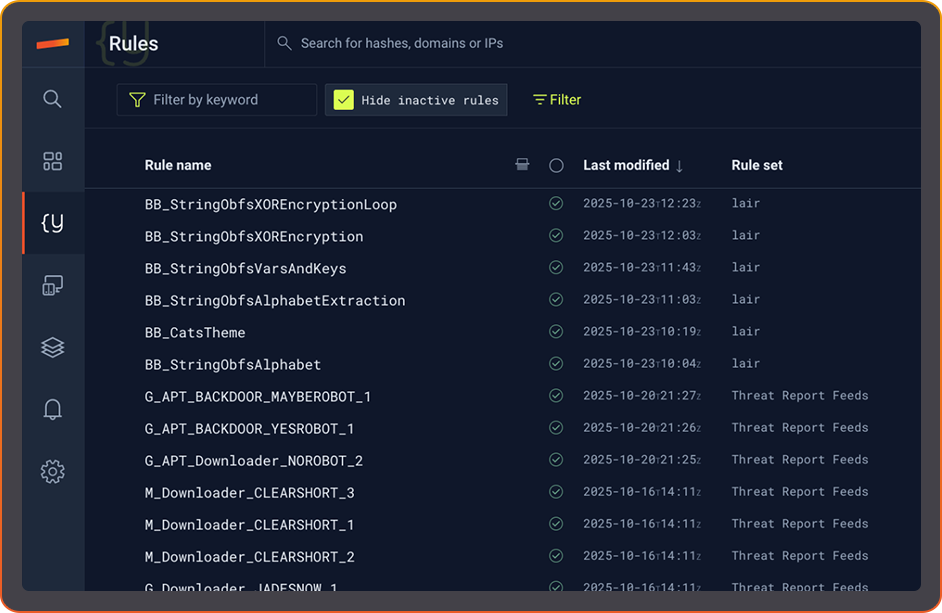
PRIVATE YARA.
FOREVER.
Stairwell runs YARA against your enterprise files in complete privacy, with nothing executed on endpoints. Scanning happens in the cloud, so devices stay untouched while you still get the signal.
Run YARA continuously across past, present, and future files to build full historical understanding and catch new matches the moment they emerge.

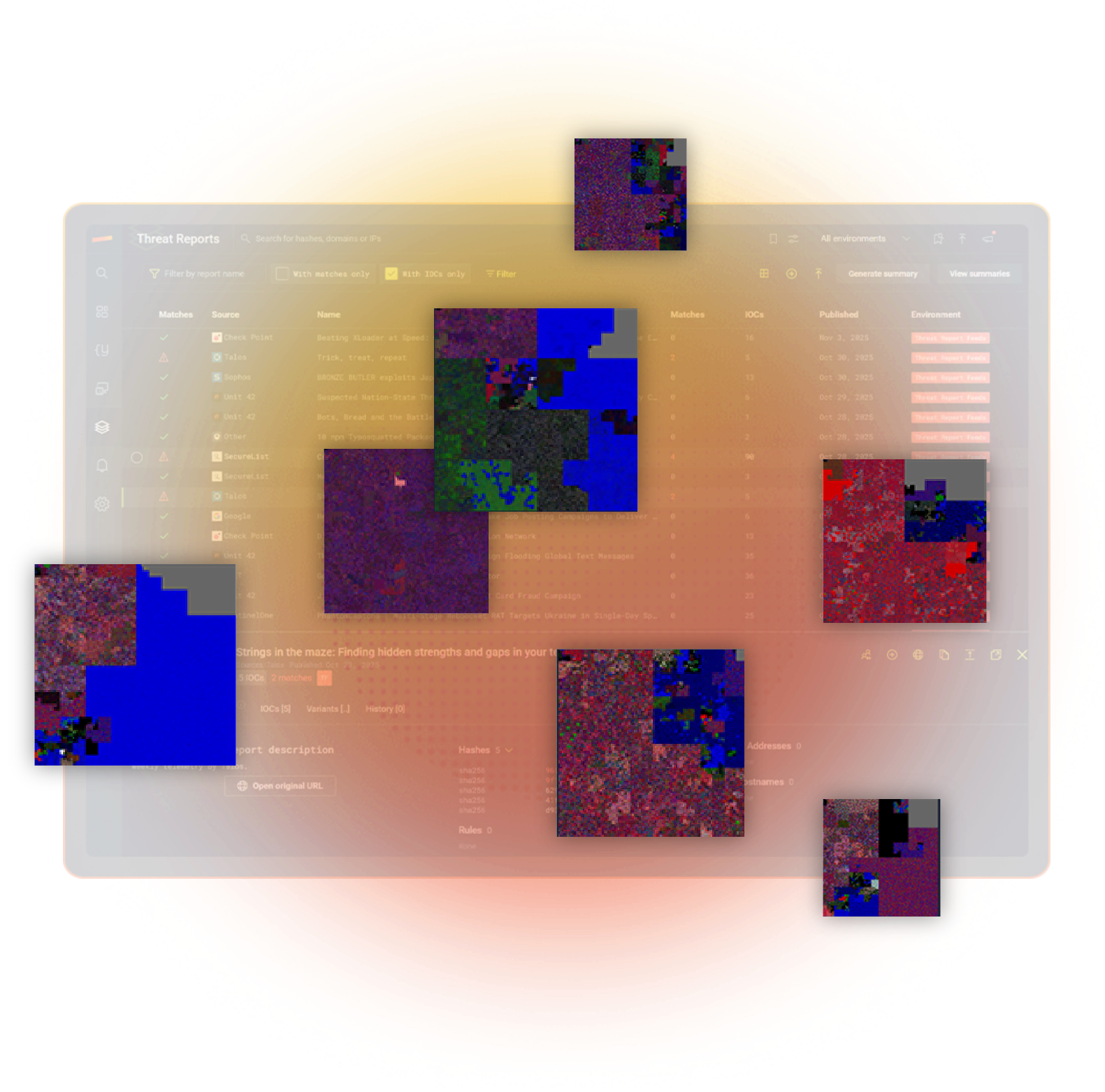
AUTOMATIC THREAT REPORT HEALTH CHECK
Immediately know if any IOC from a published threat report is in your environment. Verify exposure in seconds, not analyst hours. Stairwell does the lookup, so your team doesn’t.
Once the report is uploaded Stairwell shows which devices match any included IOCs. If nothing matches, you get a clean bill of health with a clear green check. Saves you time every day.
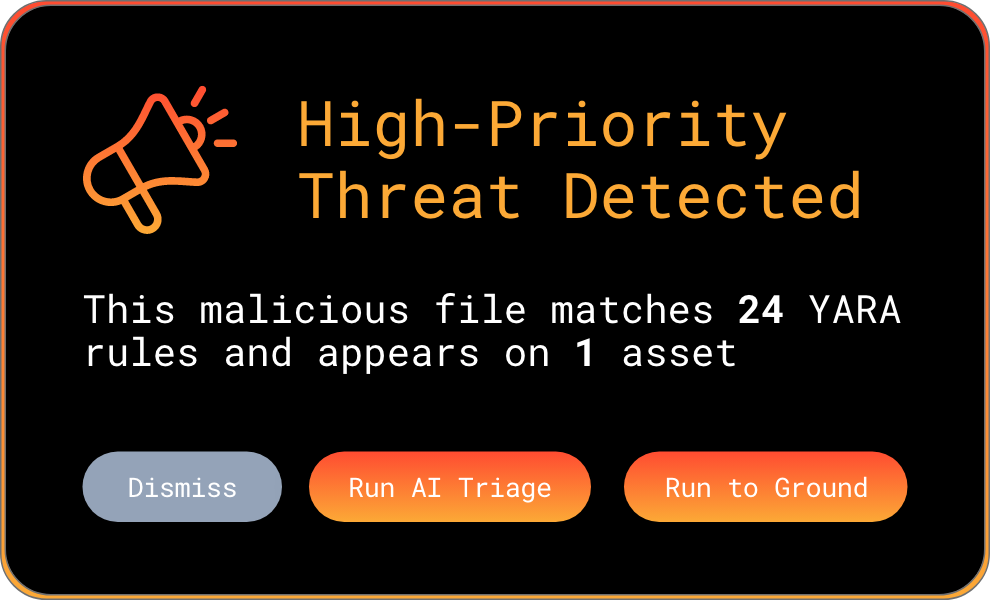
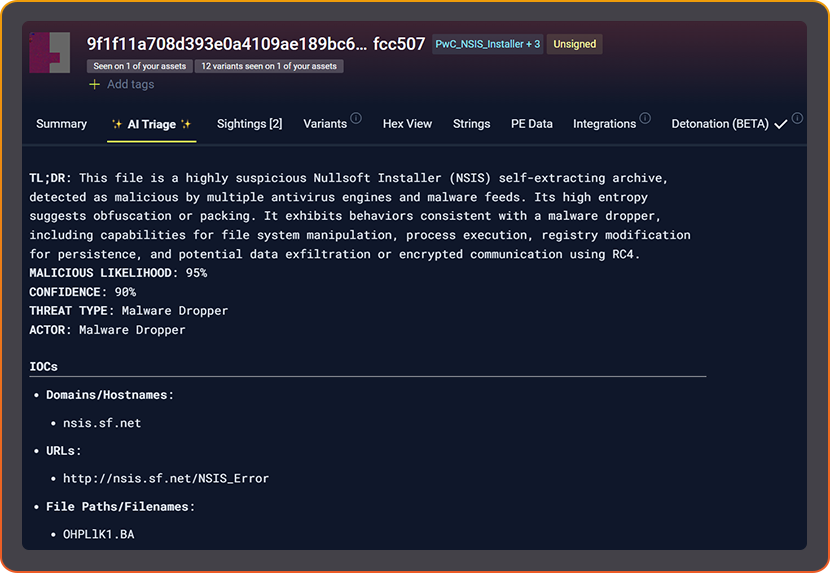
AI TRIAGE. INSTANT UNDERSTANDING.
Stairwell AI Triage analyzes what a file is built to do, using enriched context from the threat intel signals Stairwell collects at scale. It speeds up Tier 1 triage and cuts alert fatigue.
Instead of relying on generic AV pass fail checks, Stairwell explains what it does. You get the equivalent of hours of human analysis in seconds.
ENGINEERED FOR PLANET-SCALE
Built by Google and intelligence veterans. Web-scale indexing, YARA at ludicrous speed, and structured AI reasoning turn raw artifacts into instant understanding across everything you’ve ever seen.