MALWARE ANALYSIS
ANALYZE THREAT INTELLIGENCE. CONTINUOUSLY.
Static malware analysis goes stale fast as endpoints change and new executables appear every day.
Stairwell continuously reanalyzes your file history as new threat intelligence arrives, correlates signals across sources, and flags new matches you would have missed yesterday. This is threat intel you can actually use. Because it operationalizes hindsight.
HOW IT WORKS
CONTINUOUS ANALYSIS
Stairwell reanalyzes every data set continuously, so intelligence stays current.
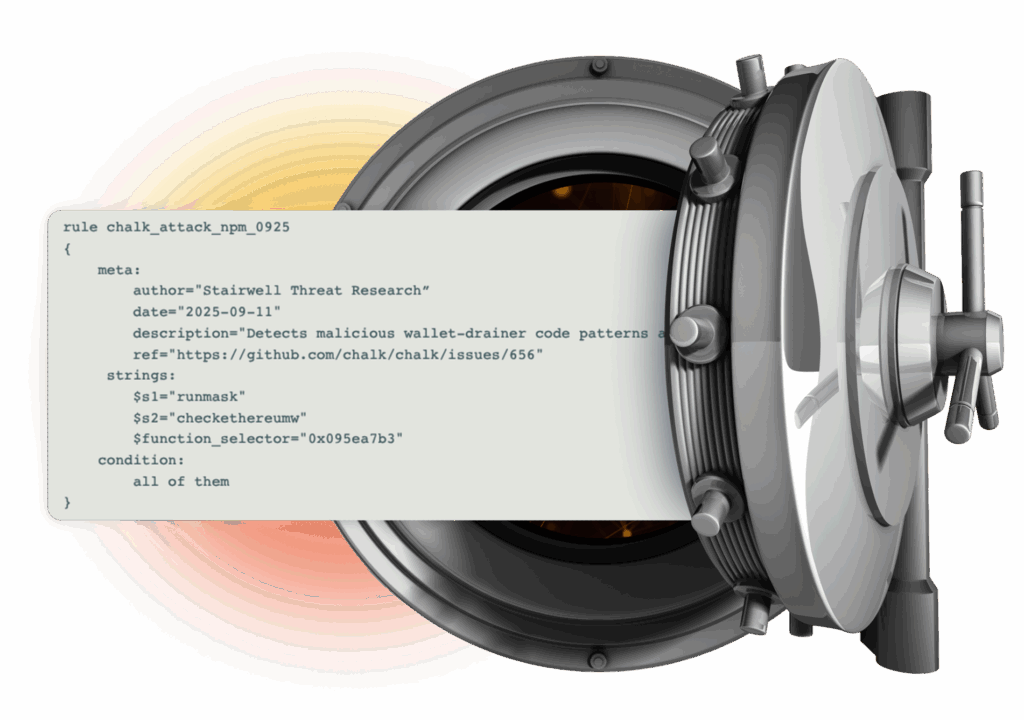
PRIVATE BY DESIGN
Stored in a private vault. Your threat intelligence stays yours, and nobody else’s.
INVISIBLE TO ADVERSARIES
Attackers reverse engineer endpoint tools, but cannot study a SaaS system they cannot access.

SEARCH ENGINE FOR THREAT INTEL
Stairwell is a private search engine for malware within your enterprise executable files. Search what matters most, your own data, to hunt threats, discover new variants, and run deep file forensics without exposing anything publicly.

PRIVATE HASH LOOKUP
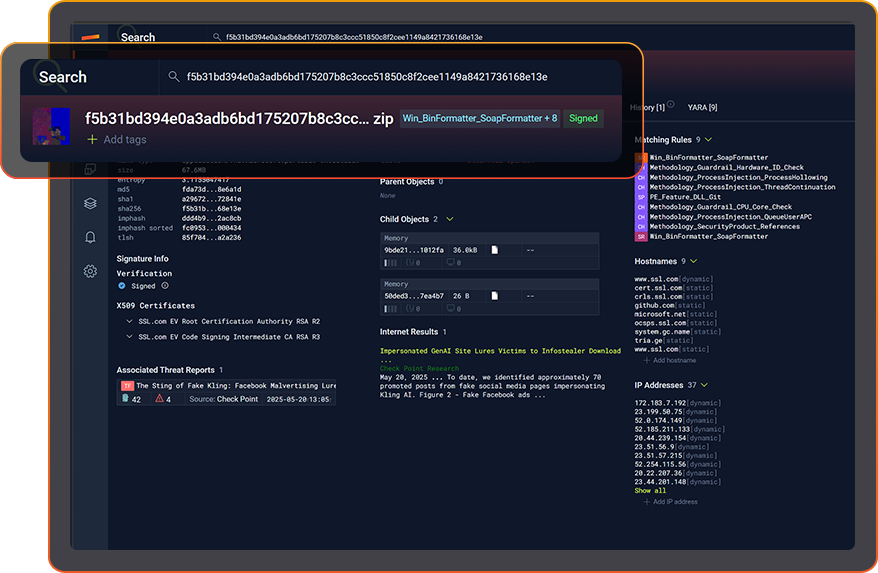
RICHER INTEL. FASTER DECISIONS.
Stairwell captures and analyzes every signal around a file, so your team stops guessing and chasing context.
Hashes, IOCs, IPs, DNS history, hostnames, YARA matches, variants, and more, all land in one place. With continuous re-analysis against newly enriched intelligence, your SOC makes faster calls with more confidence.
FIND HIDDEN VARIANTS
Stairwell uses your Private Vault plus its Malware Corpus to spot malware variants hiding inside your enterprise.
Variant Discovery turns a single hash into visibility of the entire malware family. In seconds, understand all the infrastructure this malware family used across history. No YARA required.
AUTOMATED FORENSICS. IN SECONDS.

INFECTION TIMELINE. MADE CLEAR.
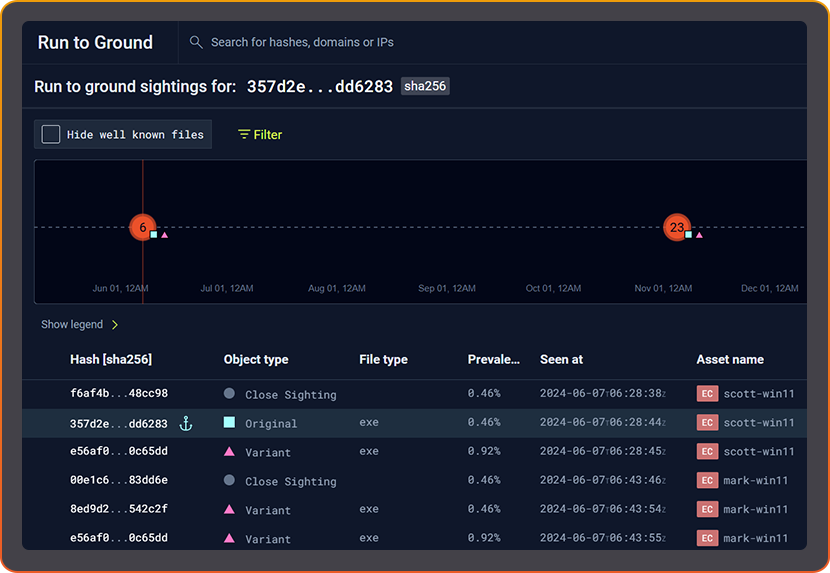
PREVALENCE. YOUR FASTEST TRIAGE SIGNAL.
Common files on every machine are rarely the problem. Rare files usually are. Stairwell continuously recalculates both local prevalence in your environment and global prevalence across Stairwell, then correlates those signals to guide what deserves attention.
By adding prevalence to your workflow, your SOC can prioritize alerts faster and cut false positives without guessing.
YARA AT SCALE
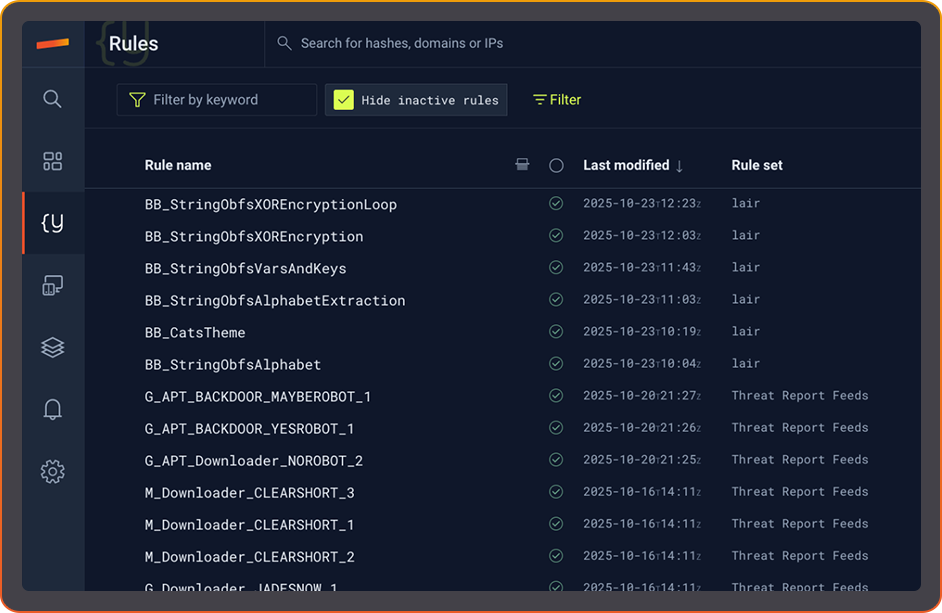
PRIVATE YARA.
FOREVER.
Stairwell runs YARA against your enterprise files in complete privacy, with nothing executed on endpoints. Scanning happens in the cloud, so devices stay untouched while you still get the signal.
Run YARA continuously across past, present, and future files to build full historical understanding and catch new matches the moment they emerge.

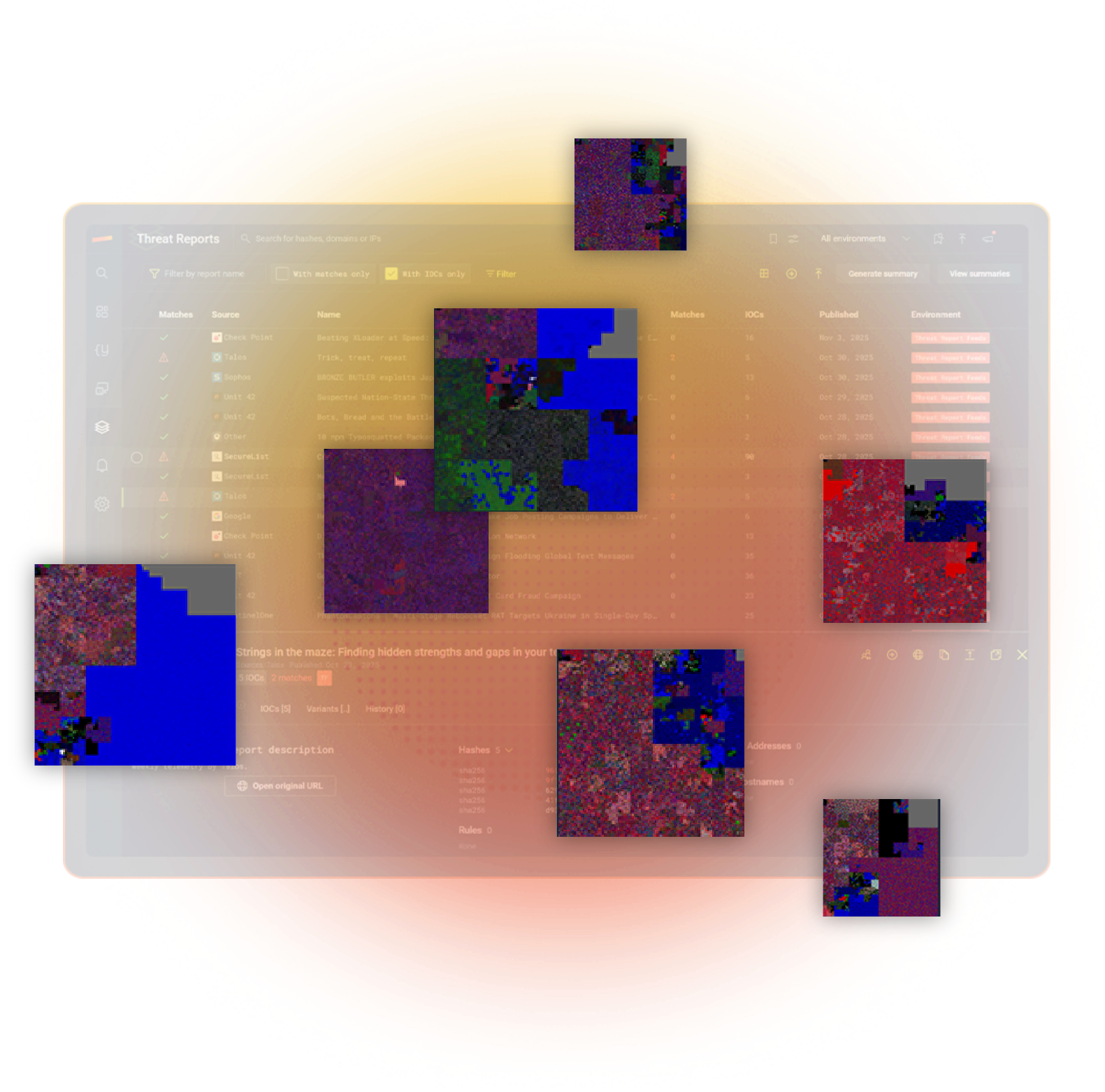
AUTOMATIC THREAT REPORT HEALTH CHECK
Immediately know if any IOC from a published threat report is in your environment. Verify exposure in seconds, not analyst hours. Stairwell does the lookup, so your team doesn’t.
Once the report is uploaded Stairwell shows which devices match any included IOCs. If nothing matches, you get a clean bill of health with a clear green check. Saves you time every day.
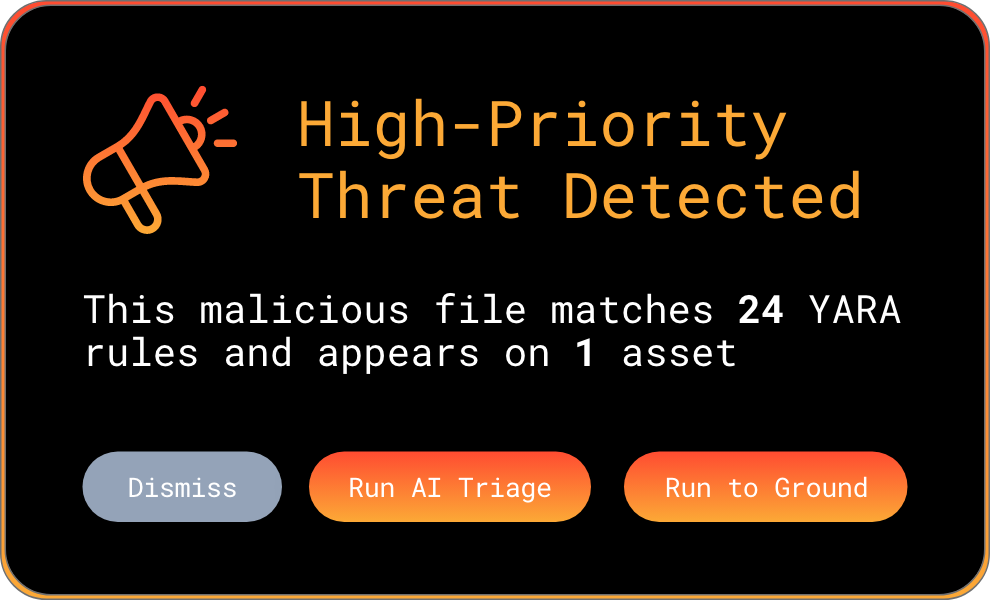
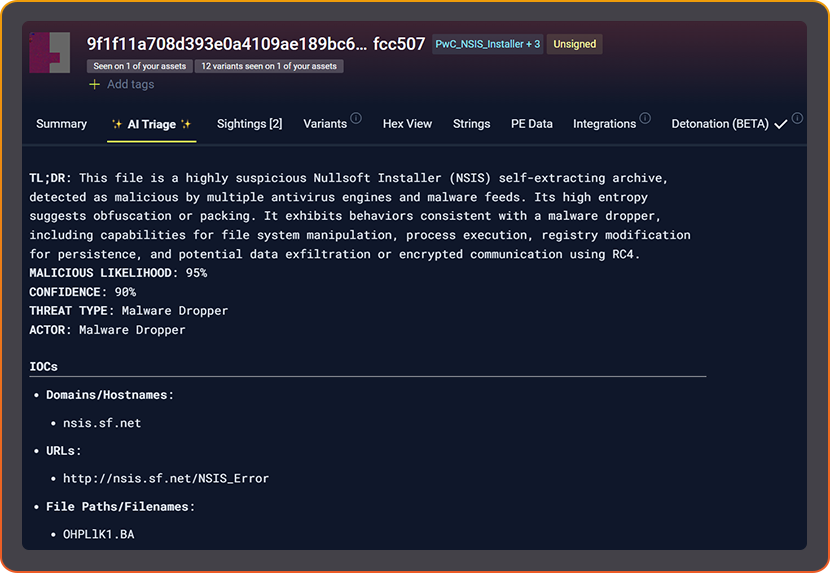
AI TRIAGE. INSTANT UNDERSTANDING.
Stairwell AI Triage analyzes what a file is built to do, using enriched context from the threat intel signals Stairwell collects at scale. It speeds up Tier 1 triage and cuts alert fatigue.
Instead of relying on generic AV pass fail checks, Stairwell explains what it does. You get the equivalent of hours of human analysis in seconds.
ENGINEERED FOR PLANET-SCALE
Built by Google and intelligence veterans. Web-scale indexing, YARA at ludicrous speed, and structured AI reasoning turn raw artifacts into instant understanding across everything you’ve ever seen.
LEARN MORE ABOUT STAIRWELL
FREQUENTLY ASKED QUESTIONS
What is static malware analysis and how does it work?
Static malware analysis examines a file’s content, structure, and characteristics without executing it. Analysts inspect file headers, imports, strings, embedded resources, code sections, and metadata to understand what the file is built to do. This approach is safe because the file never runs, making it well-suited for initial triage of unknown samples.
In practice, static analysis is faster than sandbox execution and produces signals that remain consistent regardless of environmental conditions. Tools examine characteristics like packer signatures, suspicious API calls, encoded strings, and code structure to build a picture of the file’s intent. Modern malware analysis tools like Stairwell, extend static analysis by correlating these characteristics against known malware families, enabling analysts to classify samples and identify structural similarities even when hash values differ entirely from previously seen threats.
What is the difference between static and dynamic malware analysis?
Static malware analysis examines a file without executing it, while dynamic analysis runs the file in a controlled environment (commonly called a sandbox) to observe its behavior at runtime. Static analysis is faster and reveals structural characteristics; dynamic analysis captures network connections, registry changes, file drops, and process behavior that only manifest during execution.
Both approaches have gaps. Dynamic analysis can be fooled by malware that detects sandbox environments and alters its behavior or stays dormant. Static analysis can miss obfuscated payloads that only appear at runtime. In a real investigation workflow, analysts use static analysis for initial triage and variant identification, then escalate to dynamic analysis when behavior confirmation is needed.
Stairwell’s AI Triage sits between static analysis and a sandbox. It reads file structure and behavior indicators from static characteristics, providing analysis without requiring execution, which speeds up Tier 1 SOC decisions significantly. It explains what the file is written to do.
What malware analysis tools do threat hunters use during investigations?
Threat hunters use a combination of static analysis tools, sandbox platforms, file reputation services, and threat intelligence platforms during investigations. The specific tools depend on the stage of the investigation: initial triage uses fast lookup tools, while deeper analysis requires decompilers, disassemblers, or dynamic analysis environments for complex samples.
The most effective malware analysis tools for threat hunters are those that reduce manual pivoting. When a hunter finds a suspicious file on one endpoint, they need to answer: Is this malware? Where else is it in our environment? Are there related variants in our environment?
Tools that answer these questions in a single workflow, rather than requiring multiple separate lookups or multiple human hand-offs have the biggest impact on how quickly a hunt can go from initial indicator to confirmed campaign scope.
Why does point-in-time malware analysis miss threats over time?
Point-in-time malware analysis gives you a verdict based on the threat intelligence available at the moment of submission. A file with no known signatures on day one may be definitively attributed to a known threat actor or using specific infrastructure six months later, but if your analysis stopped after the first verdict, that historical file was never re-evaluated and the connection to newer threat intelligence was never made.
This gap is most dangerous for files that arrived during an active intrusion before attribution was published. Security teams often discover months after a breach that the initial foothold was a file they scanned and cleared because the relevant YARA rule or hash match did not exist yet. Continuous re-analysis addresses this by treating new threat intelligence as a trigger to rescan your entire file history.
Stairwell reruns emerging intelligence against every file ever seen in your environment, so past unknowns become present detections when the intelligence finally catches up. Stairwell delivers continuous hindsight.
How does automated malware analysis help SOC teams manage alert volume?
Automated malware analysis reduces the time between alert generation and verdict by handling the initial investigation steps without human handoffs. When an EDR fires an alert, automated analysis can immediately check the associated file against known threat intelligence, calculate its prevalence, identify related variants, and produce a plain-language explanation of what the file does, giving the analyst a complete picture.
Alert fatigue is a real problem in high-volume SOC environments. Analysts spending thirty minutes on a file that turns out to be a benign system update and are unavailable for alerts that warrant real attention. Automated malware analysis tools work best when they return not just a verdict, but context: why is this file suspicious, what does it actually do, and what should the analyst look at next, and connect it to the files in your enterprise so you know exactly where remediation needs to happen. That context is what turns an alert into an actionable investigation rather than another item in the queue.
How does YARA work for malware analysis at enterprise scale?
YARA is a pattern-matching language that lets security researchers and analysts write rules describing the characteristics of malware: specific byte sequences, strings, code patterns, file structures, or any combination of conditions. When a YARA rule matches a file, it indicates that the file shares characteristics the rule author identified as significant, which may mean the file belongs to a known malware family or uses a particular technique.
Running YARA rules at enterprise scale requires infrastructure that can apply rules continuously across large file sets without significant performance cost. In a traditional setup, running a new rule against a file backlog requires manual effort and scheduled jobs. Platforms like Stairwell apply YARA rules continuously across the full corpus and against your enterprise files so that any new rule, whether written in-house or sourced from the community, automatically surfaces matches the moment new files arrive or as existing files are re-evaluated against new rules.
How do you use file prevalence as a malware analysis signal?
File prevalence measures how widely a specific file appears across a population of endpoints, either within your own organization or across a broader malware analysis corpus. Malware tends to be rare: it is typically designed to operate on a specific set of targets and is not the sort of file you find installed on thousands of machines by default. High rarity combined with other suspicious indicators is a meaningful signal during triage.
The value of prevalence as an analysis signal depends on having both local and global context. A file that is rare in your enterprise but extremely common globally is probably legitimate software you simply do not deploy widely. A file that is rare both locally and globally, particularly one that appeared recently and matches no known benign software catalog, deserves a much closer look. Stairwell continuously recalculates prevalence across your environment and its malware corpus, integrating that signal with file structure and threat intelligence to guide analyst attention toward genuine anomalies.