HOW IT WORKS
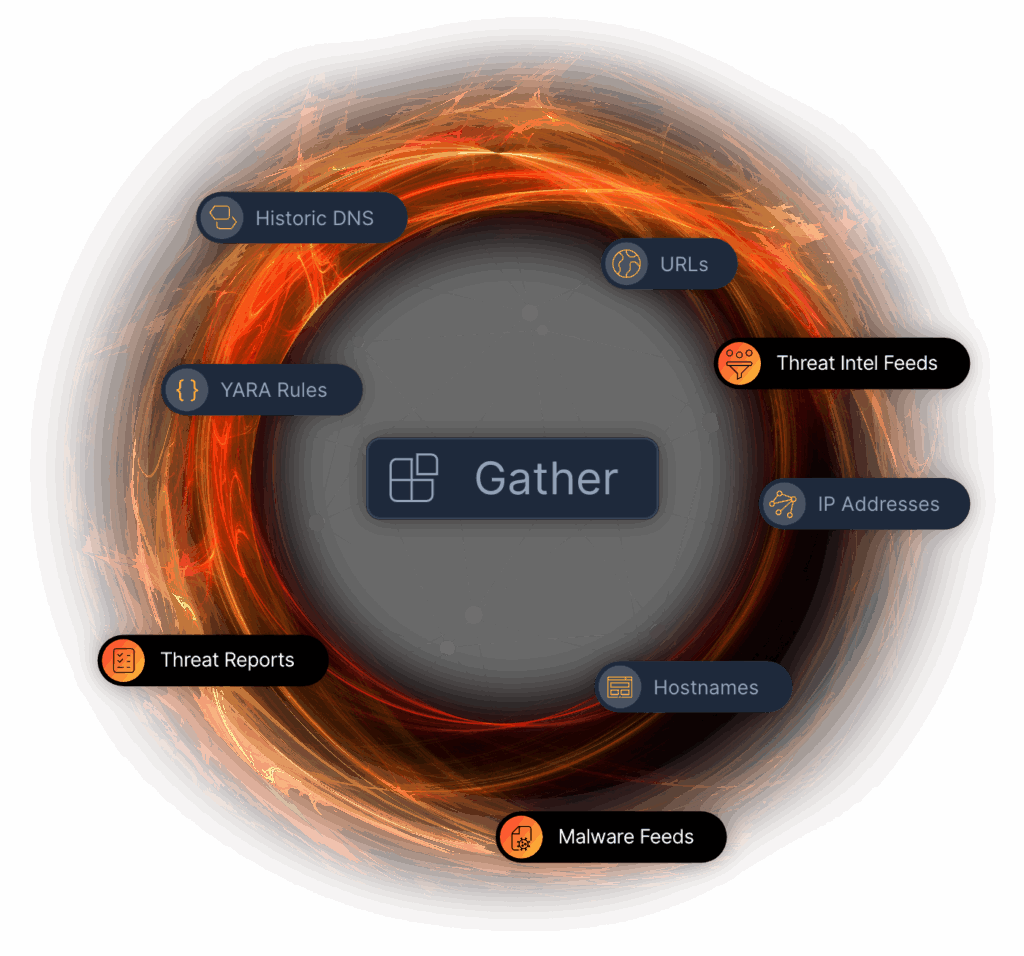
GATHER EVERYTHING.
Stairwell harvests threat intelligence from wherever it lives, including your enterprise files, threat intel feeds, DNS resolutions, EDR alerts, and published reports.
It's purposely data-agnostic, collects everything, unifies the signals, before surfacing threats across your environment faster, and more consistently, than any human.
HOW IT WORKS
CONTINUOUSLY GATHERS DATA
Continuously collects every kind of threat intelligence, including your enterprise’s files.
PRIVATE BY DESIGN
Stored in a private vault. Your threat intelligence stays yours, and nobody else’s.
INVISIBLE TO ADVERSARIES
Attackers reverse engineer endpoint tools, but cannot study a SaaS system they cannot access.
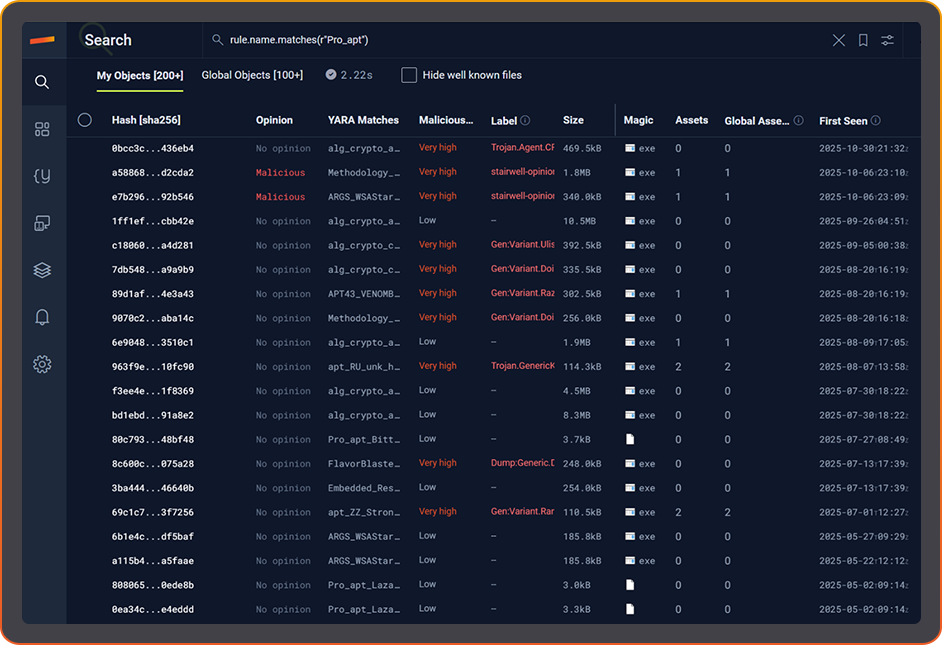
YOUR FILES.
PRIVATE VAULT
Stairwell is built for teams that cannot risk public uploads. You safely ingest and store your files in your own Private Vault, and they are never shared with anyone else.
From there, Stairwell continuously builds history and reputation on every file, so you can answer what it is, where it came from, and when it first appeared.
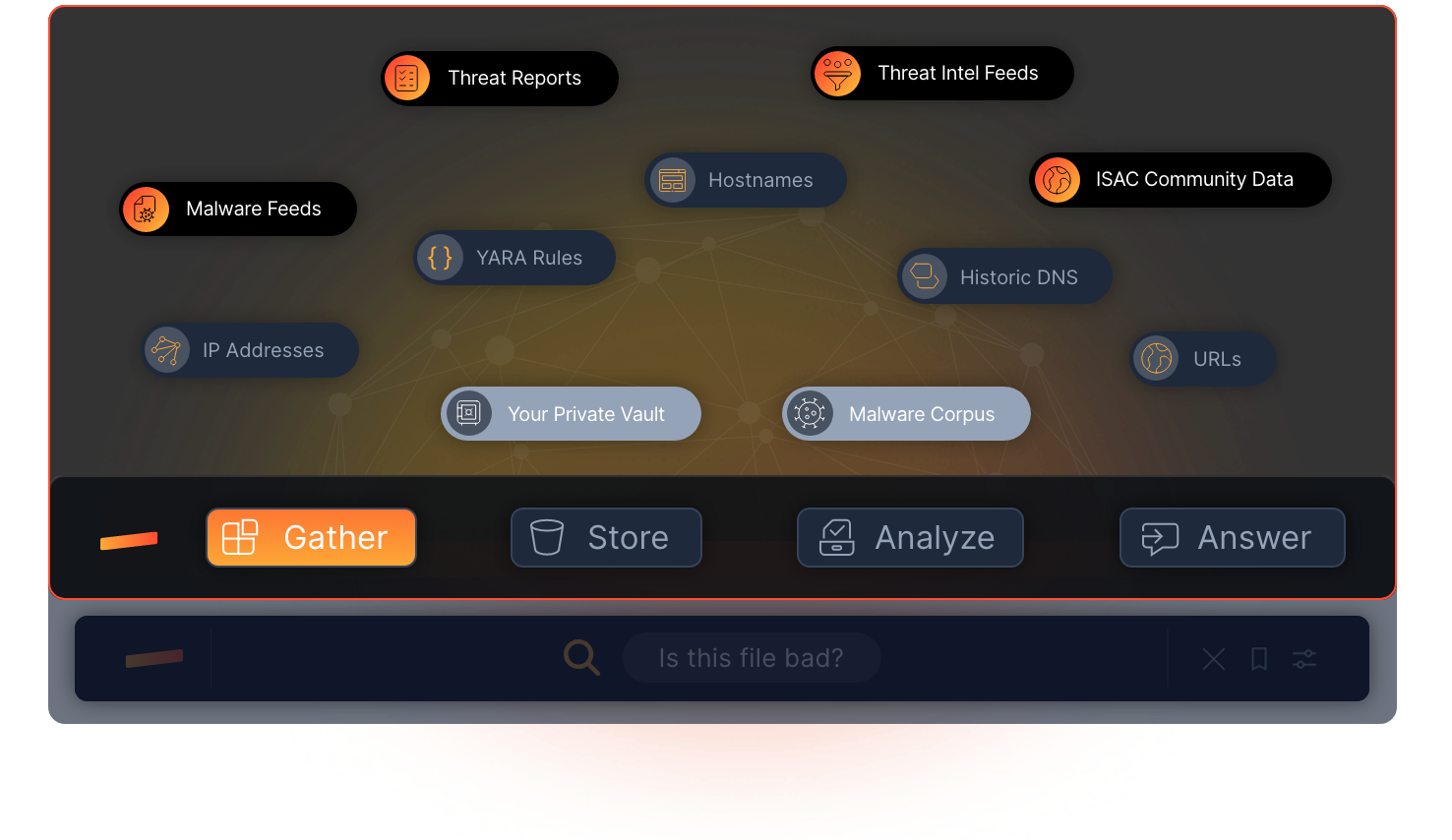
GATHER
MALWARE INTEL
Stairwell continuously ingests newly identified malware into its Malware Corpus.
The expanding corpus is then used to reanalyze every file in your Private Vault, uncovering new variants as the world changes and turning yesterday’s unknowns into today’s answers.
DIGEST PUBLISHED THREAT REPORTS
New threat reports pile up faster than any team can read them, and every one of them raises the same question: “Are we exposed or not?”
Stairwell researchers and AI agents harvest IOCs from newly published reports, load them into Stairwell, then rapidly rerun that intelligence against your enterprise files to spot previously unseen threats in your environment.
This operationalized threat intelligence saves your team hours every day.


IP & DOMAIN REPUTATION
Stairwell uses DNS resolution history to add real-world context to malware files. It continuously ingests over four billion active DNS resolutions every day, tracking IPs and domains as adversaries rotate infrastructure, so you judge reputation with current signal instead of stale guesses.
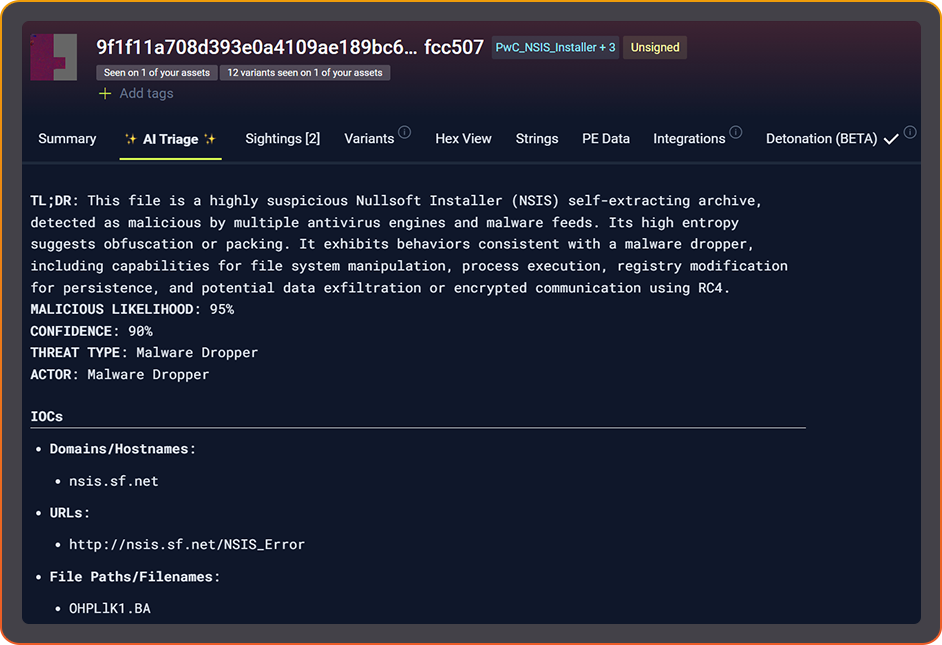
CONSUMES EDR ALERTS
Stairwell consumes your EDR alert data to automatically collect the suspicious files behind those alerts and run deeper analysis.
It gives SOC analysts a fast, independent second opinion verdict that cuts manual review time and reduces missed threats.

EASILY INGESTS
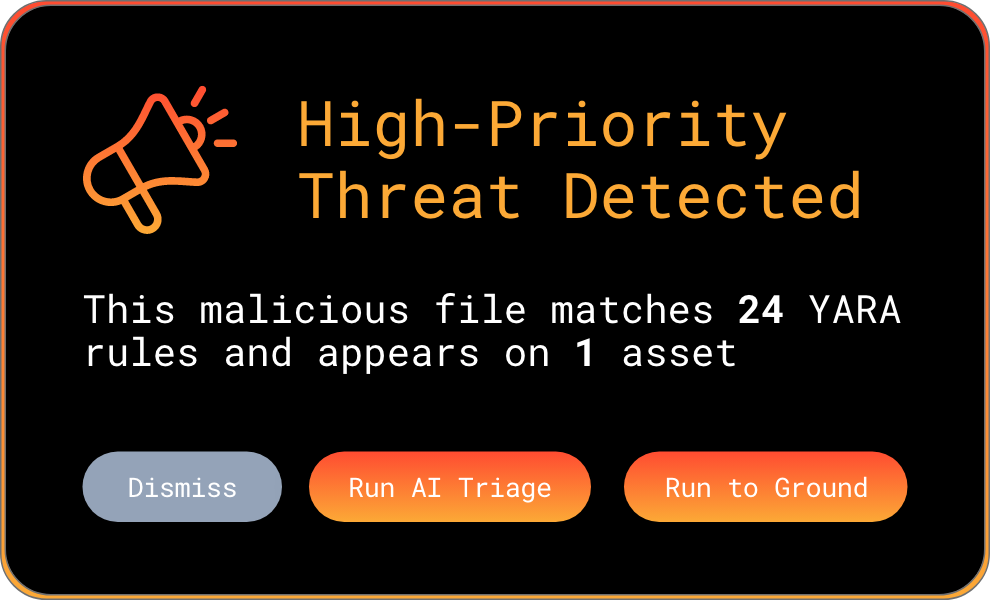
YARA RULES
ENGINEERED FOR PLANET-SCALE
Built by Google and intelligence veterans. Web-scale indexing, YARA at ludicrous speed, and structured AI reasoning turn raw artifacts into instant understanding across everything you’ve ever seen.
LEARN MORE ABOUT STAIRWELL
FREQUENTLY ASKED QUESTIONS
What are the main sources of cyber threat intelligence for enterprise security teams?
Cyber threat intelligence comes from several primary sources: commercial threat intelligence feeds, government and sector-specific information sharing groups (ISACs), open-source intelligence from public repositories and security blogs, internal telemetry from your own EDR and network logs, and published threat reports from security vendors and research teams. No single source provides complete coverage, which is why most mature security teams aggregate across multiple inputs.
The value of a threat intelligence source depends on how quickly it can be operationalized. A feed that delivers thousands of IOCs per day is only useful if your tools can automatically check those indicators against your environment and surface the ones that matter. Internal telemetry from your own endpoints is often the most actionable source because it reflects exactly what is present in your specific environment rather than what is generally observed across the industry.
How do threat intelligence feeds integrate with enterprise security operations?
Threat intelligence feeds deliver structured data containing file hashes, IP addresses, domains, and other indicators that security platforms ingest and use to enrich alerts, flag known-bad activity, and inform detection rules. Integration typically happens through a SIEM, SOAR, or a dedicated threat intelligence platform that normalizes and correlates data from multiple feeds into a unified view.
The key integration challenge is deduplication and relevance filtering. Raw feeds contain indicators that may not apply to your environment, industry, or threat model. Effective threat intelligence integration requires applying context before surfacing alerts: which indicators have appeared in your own telemetry, which match file types you actually run, and which are associated with threat actors known to target your sector. Platforms that perform this correlation automatically reduce the noise your analysts have to manage and focus attention where it matters most.
What are indicators of compromise and how are they used during investigations?
Indicators of compromise (IOCs) are observable artifacts that suggest a system has been compromised. Common IOCs include file hashes, IP addresses, domain names, registry keys, file paths, and network connection patterns associated with known malicious activity. During an investigation, analysts use IOCs to confirm whether a compromise occurred, trace how it spread, and identify related infrastructure or tooling.
IOCs have a limited shelf life because sophisticated adversaries rotate infrastructure and modify their tools specifically to invalidate known indicators. A domain used in a campaign today may be abandoned tomorrow in favor of a new one. This is why behavioral and structural indicators, such as code patterns matched by YARA rules, are increasingly important alongside traditional IOCs. Gathering both types of indicators from multiple sources, then continuously checking them against your file history, gives investigations a much stronger evidential foundation than hash-based matching alone.
Why is DNS history important for malware analysis and threat intelligence investigations?
DNS history provides a record of how domain names have resolved to IP addresses over time, which is valuable during malware investigations because it reveals the infrastructure attackers used to stage, deliver, and command malware campaigns. Knowing that a suspicious file attempted connections to a domain that recently resolved to a known malicious IP gives analysts strong corroborating evidence even when the current DNS record has been changed.
Attackers regularly rotate infrastructure to evade IP-based blocking and reputation scoring. A domain may point to a benign-looking IP today and a malicious one tomorrow. Historical DNS data lets investigators trace this rotation and connect infrastructure across campaigns even when current records look clean. Stairwell ingests more than four billion active DNS resolutions every day, building continuous resolution history that adds real-world context to file analysis and supports investigations that depend on understanding where a file was trying to communicate.
How does an organization gather threat intelligence from its own environment?
Internal threat intelligence collection starts with capturing file telemetry from endpoints: which executables, scripts, and libraries are running, when they appeared, where they came from, and which users or systems they are associated with. EDR agents typically generate some of this data, but most organizations only keep a fraction of it in logs rather than preserving the actual files for long-term analysis.
The gap between log retention and file retention matters significantly during investigations. Logs tell you a file executed; the file itself tells you what it was built to do. Organizations that collect and store the actual executables from their endpoints build a searchable history that supports threat hunting, incident response, and retrospective analysis. When new threat intelligence arrives, that file history can be re-evaluated immediately to determine whether any previously collected files match newly published indicators, turning past telemetry into a current intelligence asset.
How do YARA rules function as a threat intelligence source?
YARA rules are a form of threat intelligence that describes malware by its structural and behavioral characteristics rather than its exact hash value. When a security researcher identifies a malware family, they often author YARA rules that capture patterns present across all known variants, making it possible to detect new samples that have never been seen before but share the same underlying code or behavior.
YARA rules become most valuable as a threat intelligence source when they are applied continuously and retroactively. A new rule published after an incident can be run against your entire file history to determine whether any earlier files matched the pattern before the rule existed. This retroactive capability helps organizations understand when a threat actor first gained access to their environment, which is often weeks or months before any alert fired. Ingesting community and vendor YARA rules alongside your own private rules gives you a layered detection capability that improves over time as the collective intelligence of the security community grows. Stairwell offers lightning fast YARA rules at scale.
What is the difference between public and private threat intelligence collection?
Public threat intelligence collection involves submitting files, IOCs, or analysis results to shared platforms where data becomes available to the broader security community. This approach benefits from crowd-sourced coverage: more submissions mean more indicators, and more analysts reviewing data means faster attribution. The tradeoff is that your submissions disclose information about what threats you have encountered, what tools you use, and potentially what systems you run.
Private threat intelligence collection keeps your file telemetry, analysis results, and custom detection rules inside your own environment or a designated private vault. This approach protects operational security: adversaries monitoring public platforms cannot determine whether you have detected their tools. It is also essential for regulated industries where submitting file data to third-party services may violate data handling requirements. The practical challenge with private collection is resource intensity; you need a platform that can analyze and enrich your private data at scale without relying on crowd-sourced verdicts to fill gaps.