THREAT REPORTS
THREAT INTEL: CONFIRMED
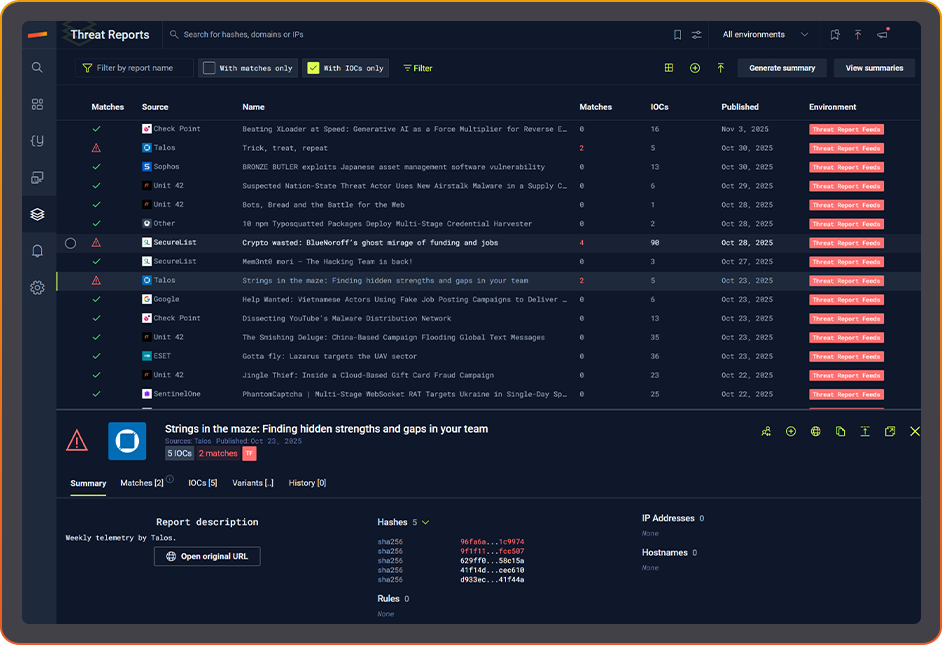
Immediately know if any indicator of compromise from a published threat report is in your environment. Verify exposure in seconds, not analyst hours.
Stairwell does the lookup, so your team doesn't.

PUBLISHED THREAT REPORTS:
AUTOMATED IOC HEALTH CHECK
BETTER SECURITY OPERATIONS
Connect new threat intel to your files the moment it’s published
FROM REPORT TO REALITY
Know the presence or absence of an IOC inside your enterprise.
PREVENT ANALYST BURNOUT
Automation focuses your SOC analyst only on IOCs found in your environment.
INTELLIGENCE GATHERED. AUTOMATICALLY.
The flood of weekly threat reports is constant. Chasing them and copy-pasting IOCs to see if they touch your environment burns analyst hours you don’t have.
Stairwell’s researchers and AI agents harvest IOCs as reports drop, load them into your private vault, and auto-check them across your entire file history.

THREAT REPORTS. OPERATIONALIZED.
With a comprehensive living library of thousands of published threat reports, Stairwell has operationalized threat reports and the IOCs they contain to save you hours every day.
We automatically check those IOCs against your file history to confirm presence or absence across your environment with no manual lookups.
When you’re in the clear, you’ll see it: a simple green check that your organization is unaffected.
CREATE YOUR OWN THREAT REPORTS
Upload your own IOCs to Stairwell in a custom Threat Report. Building your own is easy and keeps you aware of any specific IOCs your organization is tracking.
Connect your own threat report intelligence to your files to determine the presence or absence instantly. With continuous re-analysis, your enterprise is always up to date.


FROM REPORTS TO HIDDEN VARIANTS
ENGINEERED FOR PLANET-SCALE
Built by Google and intelligence veterans. Web-scale indexing, YARA at ludicrous speed, and structured AI reasoning turn raw artifacts into instant understanding across everything you’ve ever seen.
LEARN MORE ABOUT STAIRWELL
FREQUENTLY ASKED QUESTIONS
What is a malware threat report and what does it typically contain?
A malware threat report is a published document from a security vendor, government agency, or research team that documents a specific malware campaign, threat actor, or vulnerability. These reports typically include indicators of compromise (file hashes, IP addresses, domains), a technical analysis of the malware’s capabilities and behavior, attribution assessments, and recommendations for detection and remediation.
The value of a malware analysis report depends heavily on how quickly the intelligence within it can be operationalized. A report that lists twenty file hashes and thirty domains is only useful if your team can rapidly determine whether any of those indicators appear in your environment. Manually copying IOCs from a PDF and querying each one is a slow, tedious, and error-prone process.
Automated ingestion and cross-referencing, where the platform harvests IOCs from newly published reports and immediately checks them against your file history, transforms a research document into an operational tool. Automatically being able to prove both presence or absence of a threat in your enterprise is how threat intelligence ideally gets operationalized.
How do security teams operationalize threat report IOCs without spending hours on manual lookups?
Operationalizing threat report IOCs automatically requires a platform that ingests reports as they are published, extracts the IOCs they contain, and immediately checks those indicators against your enterprise file history and telemetry. This removes the manual step of parsing PDFs, extracting hashes, and running individual lookups that consumes analyst time in most SOC environments.
The typical workflow without automation involves an analyst reading a new threat report, copying each indicator, querying it individually against the SIEM or a hash lookup service, documenting the results, and compiling a status report for leadership. That process takes hours per report, and reports arrive daily. Platforms that maintain a library of threat report IOCs and automatically cross-reference them against your environment let your team skip directly to investigating actual matches rather than executing the lookup pipeline manually for every published report. This is a feature included in Stairwell’s platform.
How do you quickly determine whether IOCs from a newly published threat report appear in your environment?
The fastest way to check threat report IOCs against your environment is to use a platform that has already ingested the report and automatically queried its indicators against your file history. If the platform maintains a continuous library of published reports, the check runs immediately when the report is added, before any analyst has even opened it, and the result is a clear exposure status: affected or clean.
Manual IOC checking is one of the highest-volume, lowest-value activities in a threat intelligence team’s day. It requires no judgment or expertise; it is pure lookup work. Automating this step frees analysts to do the work that actually requires their experience: investigating genuine matches, hunting for related threats, and building detection rules for the indicators the automated check surfaced. When the result is clean, the system provides documented confirmation that the organization was not exposed, which is itself valuable for compliance and executive reporting purposes.
What is the difference between a threat report and actionable threat intelligence?
A threat report is a document; actionable threat intelligence is the result of connecting that document’s indicators to your specific environment. A report that details a sophisticated ransomware campaign is useful background reading. Knowing that three of the listed file hashes appeared on two of your endpoints last month is intelligence your team can act on immediately.
The gap between information and action is where most threat intelligence programs lose value. Organizations that consume dozens of reports per week often find that very little of what they read translates to changes in their detection posture or their investigation workflow because the connection between the published intelligence and their own environment is never systematically made. Platforms that automatically close this gap by running report IOCs against enterprise telemetry as reports are published convert passive threat report consumption into active threat intelligence operations.
How do published threat reports support proactive threat hunting activities?
Published threat reports give threat hunters structured starting points for hypotheses: if a particular threat actor uses a specific set of TTPs or a known toolset, hunters can search their environment for behavioral or structural evidence of those same techniques. Reports provide the vocabulary of attack patterns that hunters translate into queries, YARA rules, and behavioral detections.
The limitation of relying solely on published reports for threat hunting is that reports describe threats that have already been observed and documented elsewhere. By the time a report is published, the indicators it contains may already be stale, and the more capable threat actors will have moved on to new infrastructure or modified their tooling. Hunters who combine published report intelligence with structural similarity analysis can extend coverage beyond the exact indicators in the report to find related variants and updated versions of the same toolset that the report does not specifically describe.
Why do published threat reports typically miss a significant number of malware variants?
Published threat reports document the specific samples that researchers analyzed, but they rarely achieve comprehensive coverage of the entire malware family. Researchers work from samples they encounter or receive, and many variants of a malware family circulate in the wild without ever reaching the corpus that a particular research team examines. This means any given report reflects a subset of total activity, not the complete picture.
Analysis by Stairwell on published threat reports found that, on average, applying variant discovery to the samples listed in a report uncovers more than 20 additional related malware variants per report that were not included in the original publication, representing roughly 157% more samples than the report documented. For security teams relying on report IOCs for detection coverage, this gap means that blocking or hunting for only the listed samples leaves a significant proportion of the malware family undetected. Going beyond the listed indicators to search for structurally related samples closes that coverage gap.
How do you build a custom threat report to track organization-specific IOCs?
A custom threat report is an internal collection of indicators specific to threats your organization is actively tracking, such as infrastructure associated with a known attacker targeting your industry, file hashes from a past incident, or domains identified during a previous investigation. Unlike published reports, a custom report captures intelligence that is specific to your threat model and is not shared outside your organization.
Custom reports are most useful when they are connected to continuous analysis rather than treated as static lists. When a new file appears in your environment that matches an indicator in your custom report, the detection should trigger automatically without requiring an analyst to periodically re-run the lookup manually. Platforms that support custom threat report creation and apply those IOCs continuously against your enterprise telemetry keep your organization-specific intelligence operational over time, ensuring that actors you have previously identified do not re-enter your environment undetected.