Stairwell recently identified a significant and concerning trend across our customer base: over 80% of monitored environments contain vulnerable versions of WinRAR affected by CVE-2025-8088.
This finding underscores a persistent challenge in enterprise security when widely deployed, trusted software that quietly falls out of date and becomes a high-value target for attackers.
The Risk: CVE-2025-8088 in WinRAR
Google identified the exploitation of CVE-2025-8088 that impacts Windows versions of WinRAR earlier than 7.13, a range that spans many years of releases. WinRAR remains one of the most commonly installed archive utilities in enterprise and developer environments, often persisting long after its initial installation.
Because WinRAR is frequently used to handle untrusted archives received via email, download portals, or shared file systems, vulnerabilities in the application are especially attractive for exploitation. Attackers can reliably assume its presence and leverage it as an initial access or execution vector.
How Stairwell Identified the Exposure
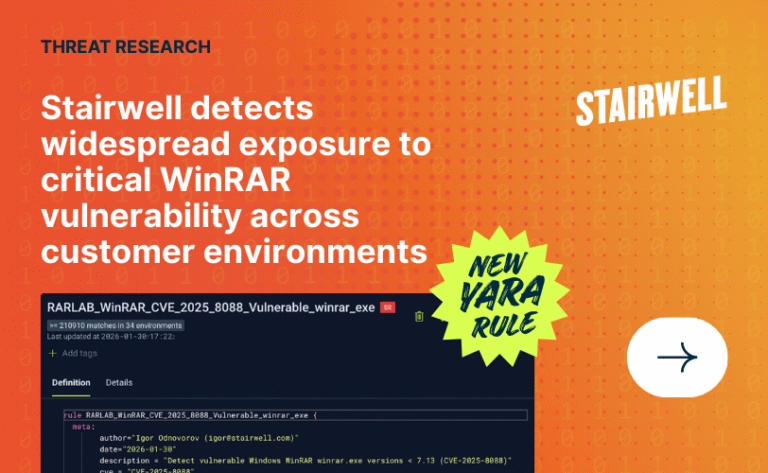
Stairwell uses behavioral telemetry and high-fidelity content inspection to surface latent risk across customer environments. To detect vulnerable WinRAR installations, our research team authored a targeted YARA rule designed to identify:
- Windows PE executables
- Identified as winrar.exe
- Reporting WinRAR versions earlier than 7.13
rule RARLAB_WinRAR_CVE_2025_8088_Vulnerable_winrar_exe {
meta:
author="Igor Odnovorov (igor@stairwell.com)"
date="2026-01-30"
description = "Detect vulnerable Windows WinRAR winrar.exe versions < 7.13 (CVE-2025-8088)"
cve = "CVE-2025-8088"
reference = "https://nvd.nist.gov/vuln/detail/CVE-2025-8088"
condition:
pe.is_pe
and pe.version_info["ProductName"] matches /winrar/i
and (
pe.version_info["ProductVersion"] matches /^[0-6]\./i or
pe.version_info["ProductVersion"] matches /^7\.(0?[0-9]|1[0-2])(\.|$)/i
)
}
What We Found
When deployed across Stairwell customer environments, this detection revealed that more than four out of five organizations still had at least one vulnerable WinRAR binary present.
There are many reasons how this could happen including the file being:
- Identify exactly where vulnerable WinRAR binaries exist
- Prioritize remediation based on exposure and usage
- Track progress as vulnerable artifacts are removed or updated
- Validate that golden images and build pipelines are clean going forward
Final Thoughts
CVE-2025-8088 is a reminder that security debt accumulates quietly. Widely trusted tools like WinRAR often escape scrutiny precisely because they are so familiar.
Stairwell’s detection of vulnerable WinRAR versions in over 80% of customer environments demonstrates the value of deep, content-aware visibility, and the importance of proactively hunting for risk, not just responding to alerts.
All Stairwell customers were made aware exactly which devices were affected.
If you’d like to learn more about how Stairwell identifies hidden vulnerabilities and long-tail risk across your environment, reach out to our team or explore our research.