INCIDENT RESPONSE
RUN EVERY ALERT TO GROUND
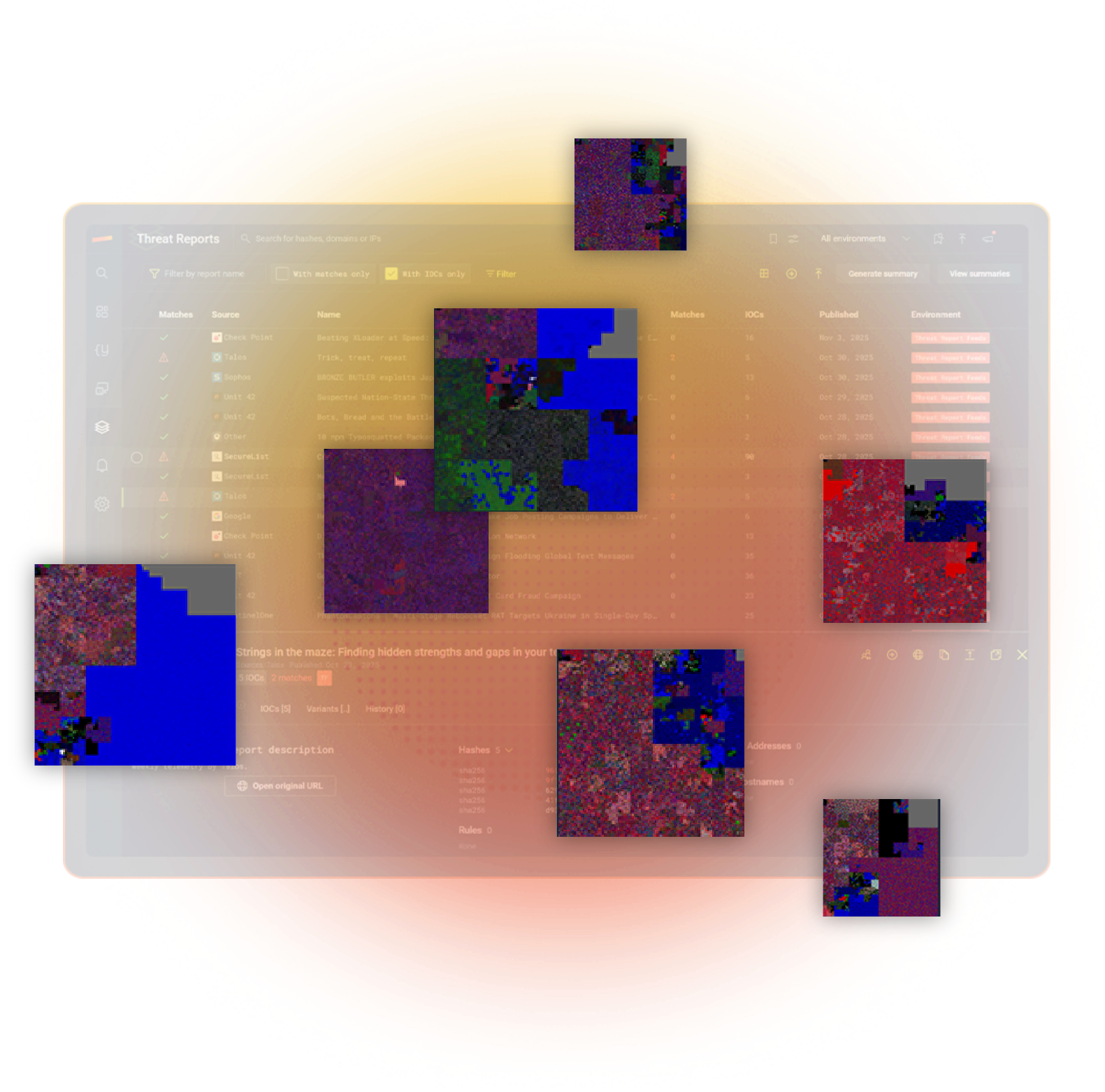
Run to Ground turns any alert, indicator of compromise, or file into a full incident response campaign view. It connects variants, endpoints, and timelines in one place, so you can prove blast radius, trace infection paths, and close the loop with evidence.
WHY RUNNING ALERTS TO GROUND MATTERS
BEYOND SINGLE ALERTS
Stairwell turns a single alert into linked files, hosts, users, and infrastructure so you can run every threat to ground.
UNDERSTAND BLAST RADIUS
Stairwell maps where a threat has and hasn’t been, so you know real impact from the truth of your own data.
MANUAL PIVOT FATIGUE
Automates manual pivots from EDR, SIEM, DNS, and threat feeds into one investigation view, saving your team time.
“Stairwell has accelerated our threat response and enhanced accuracy. The run to ground feature provides comprehensive visibility into related files, empowering us to respond more effectively and protect our organization with greater certainty.”
Tony Watson, CISO, Groq
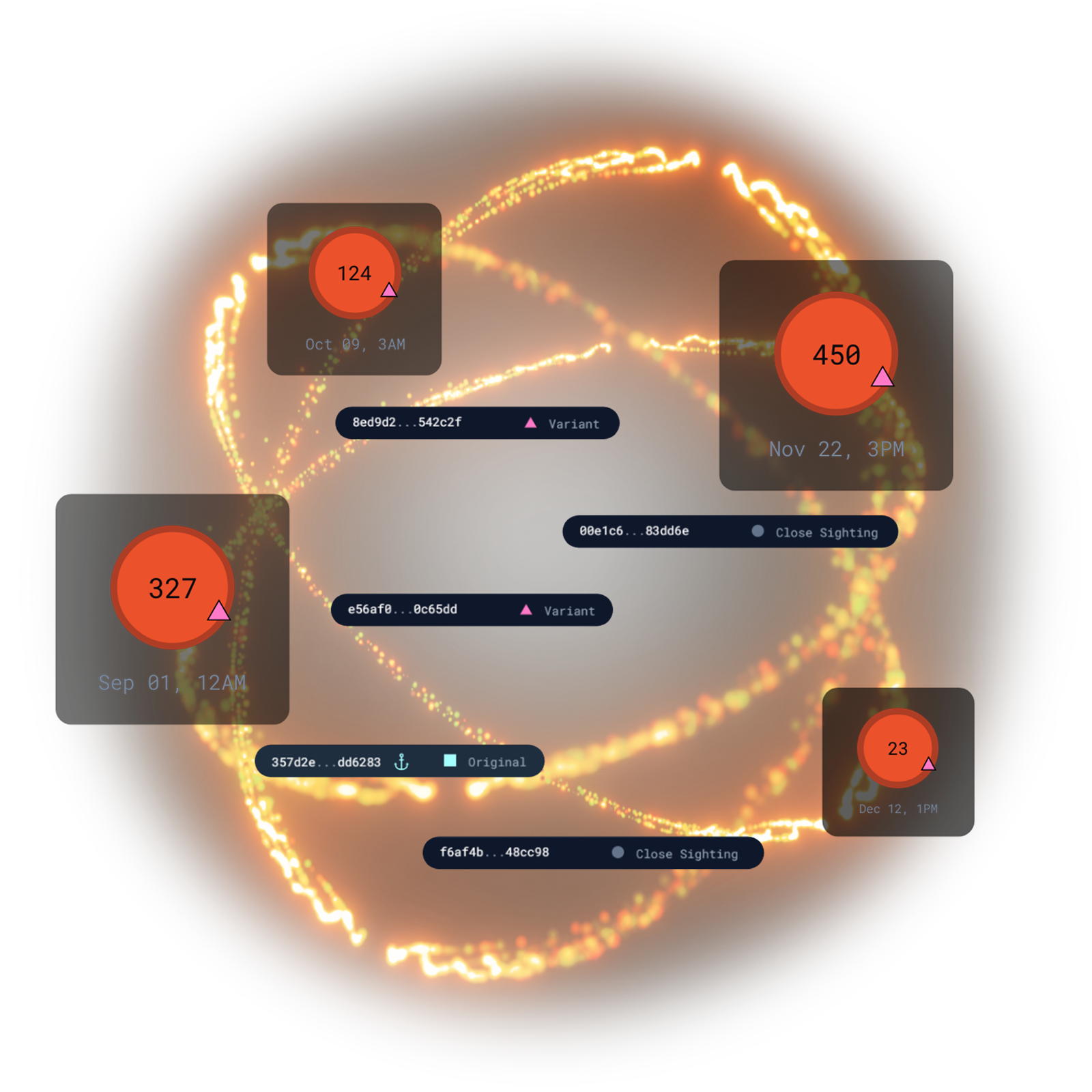
WHAT IS RUN TO GROUND?
IOC TO CAMPAIGN IN ONE CLICK
- Finds files related by structure and content, not just exact hash matches
- Sees every host touched, whether the file executed or misbehaved
- Connects artifacts including linked domains, IPs, and C2
- Identifies droppers, loaders, and second-stage payloads by analyzing low-prevalence files that appear within 24 hours of each variant.

FROM FILE TO FULL SCOPE
- Identifies which devices possessed the file, even if it didn’t execute.
- Shows paths to where the file is on disk, revealing user directories and staging locations
- Finds reuse patterns and lateral movement across systems

ONE SAMPLE TO ENTIRE FAMILY
- Expand from one sample to every repacked, re-signed, and modified variant
- See how each variant spread across hosts and time
- Find connections to threat reports, YARA rules, and shared infrastructure
ENGINEERED FOR PLANET-SCALE
Built by Google and intelligence veterans. Web-scale indexing, YARA at ludicrous speed, and structured AI reasoning turn raw artifacts into instant understanding across everything you’ve ever seen.